Date : 06 Mar, 2025
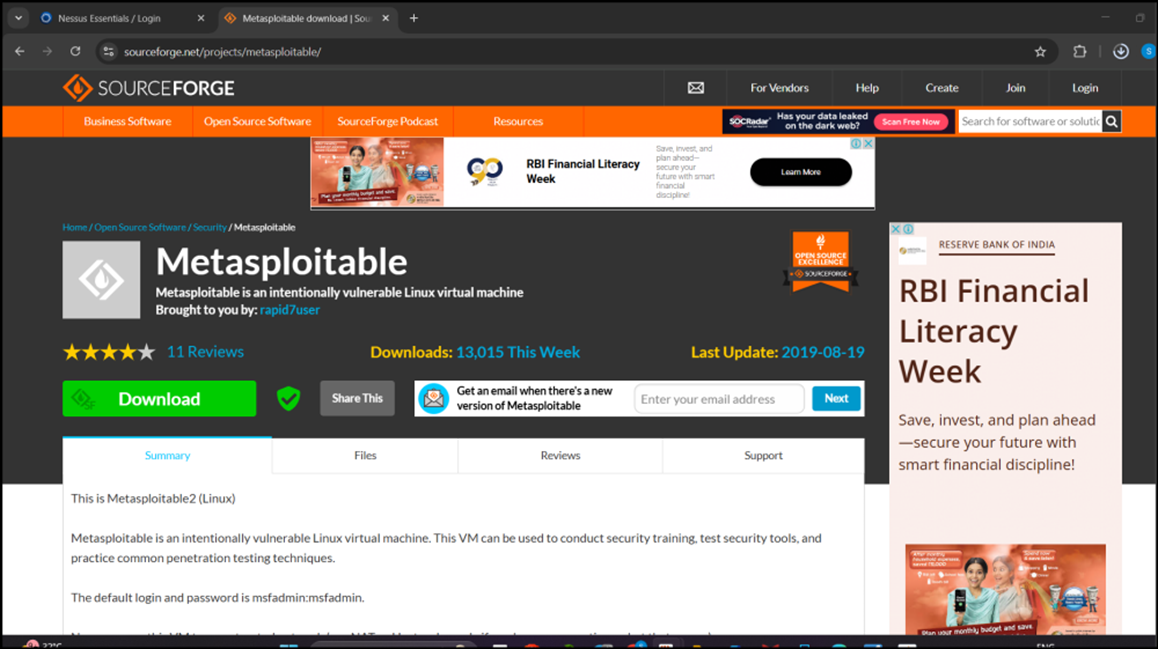
[Download Metasploitable](https:// sourceforge.net/projects/metasploitable/)
-
extract all → then open the vmx file in vmware
-
username : msfadmin,password :msfadmin
-
ifconfig
- this will get you the ip of metasploit, which is the target ip
-
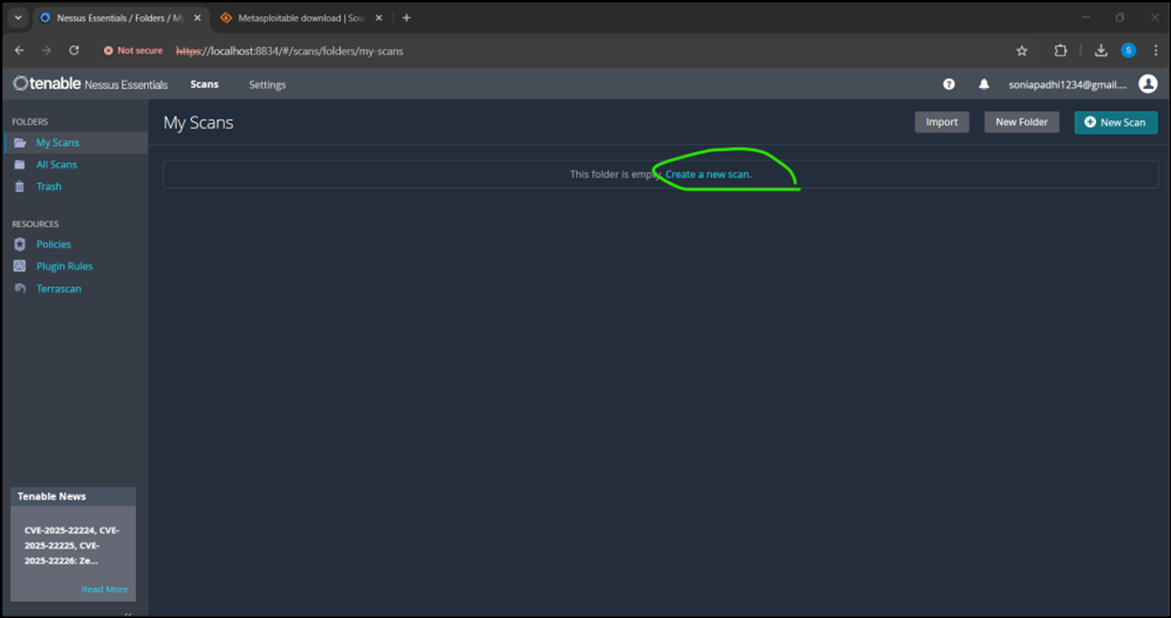
Create a new scan in nessus
-
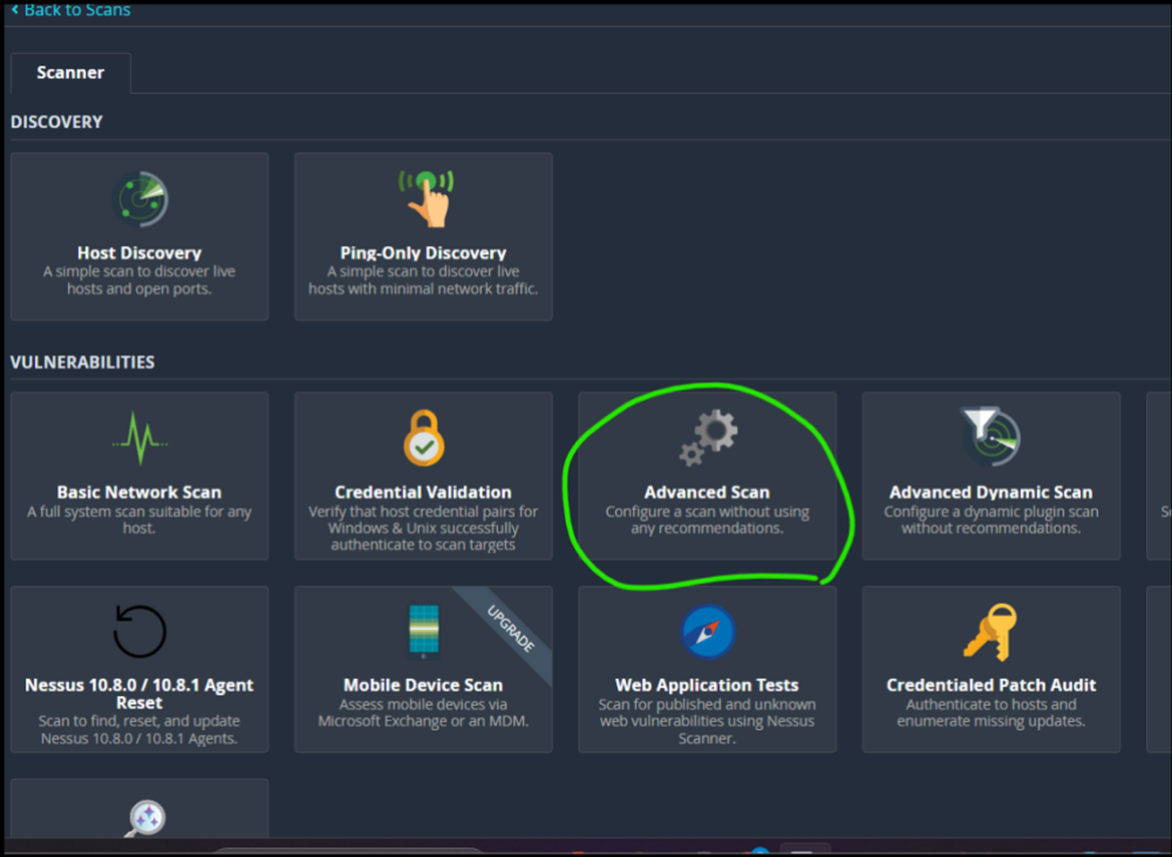
Advanced scan
-
Fill the following details
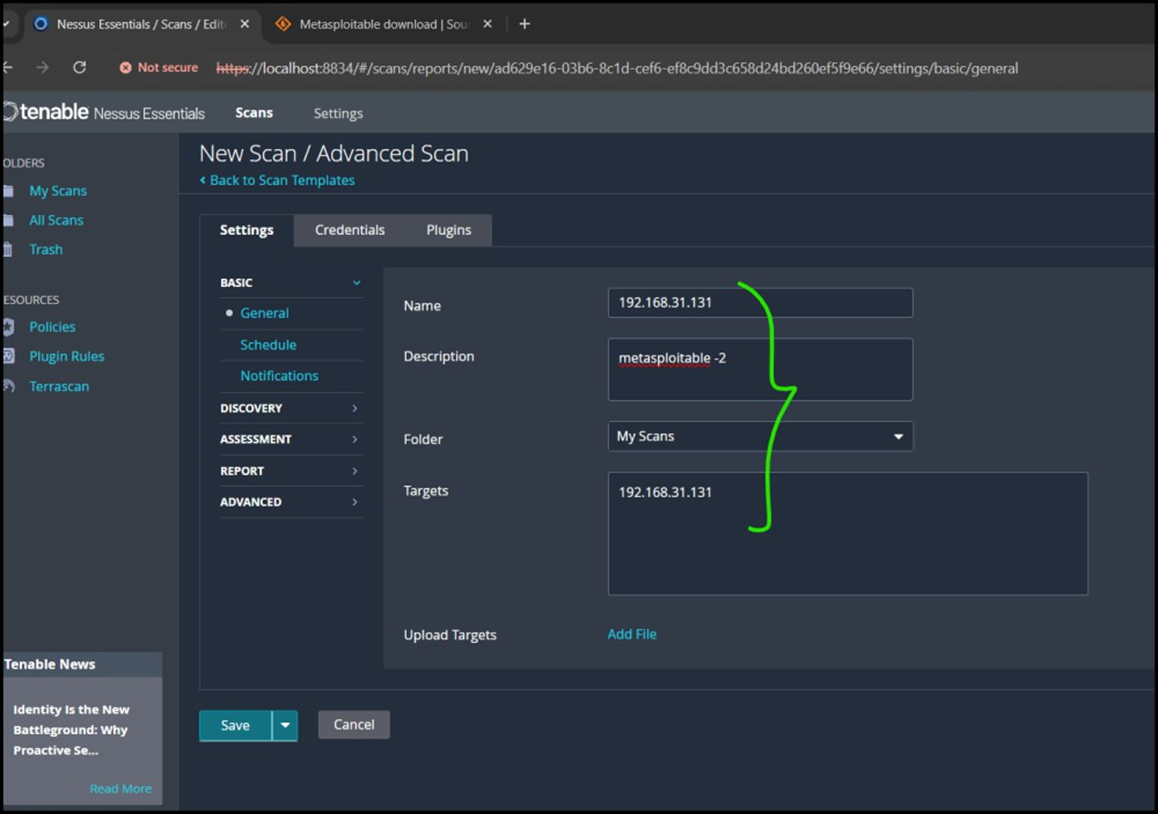
-
Discovery→host discovery→ do the following edits
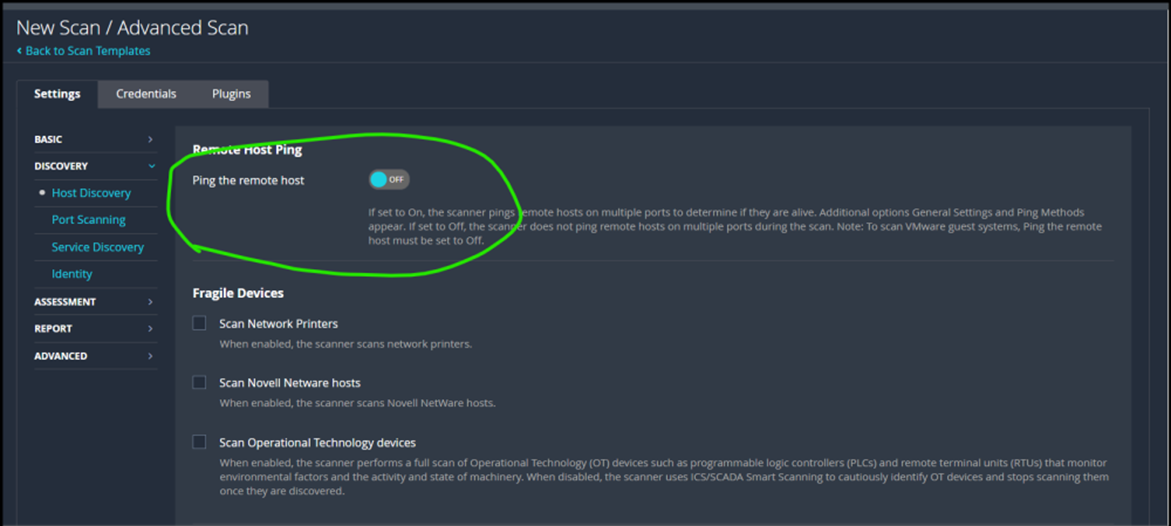
-
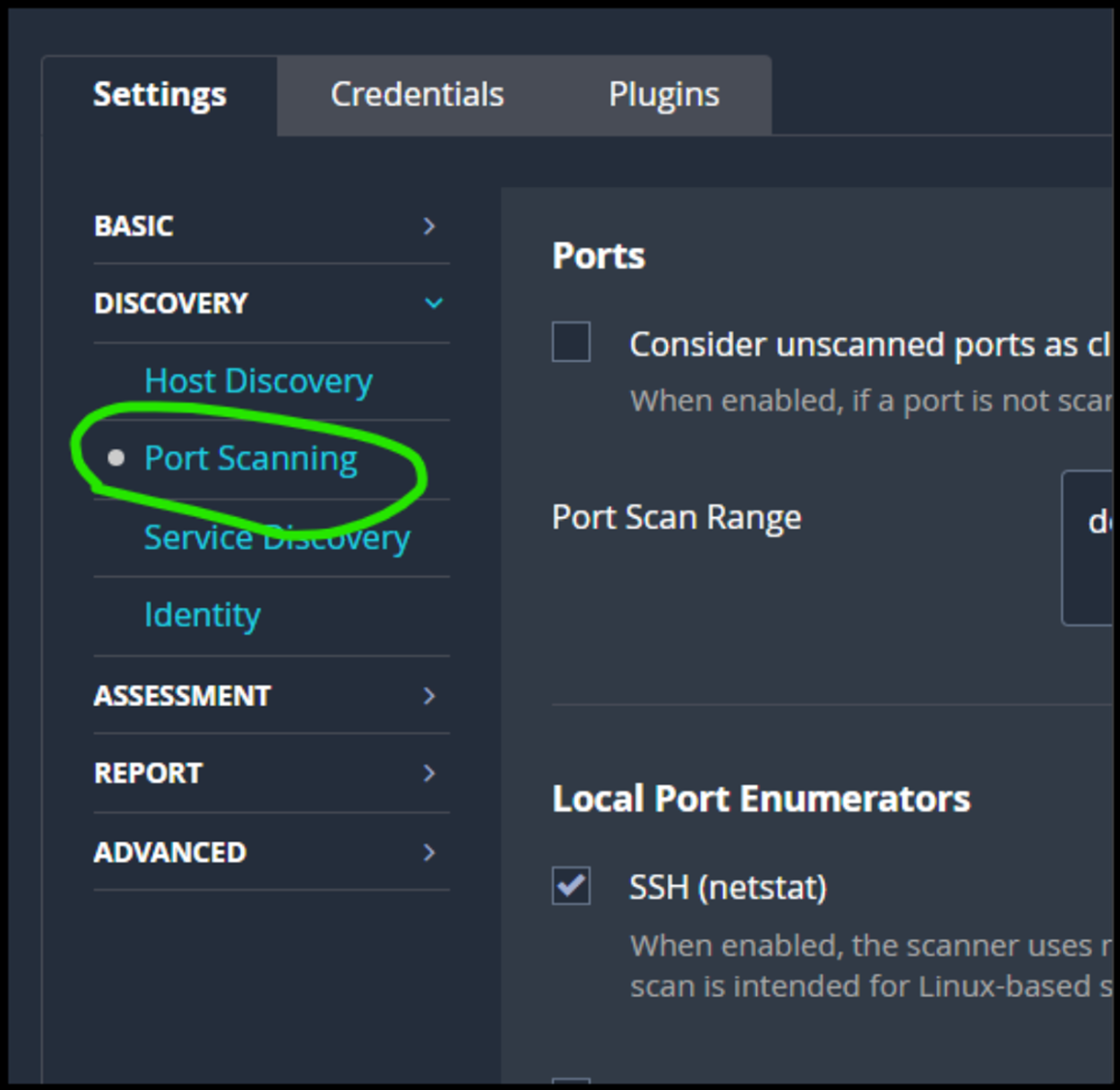
Go to
port scanning
-
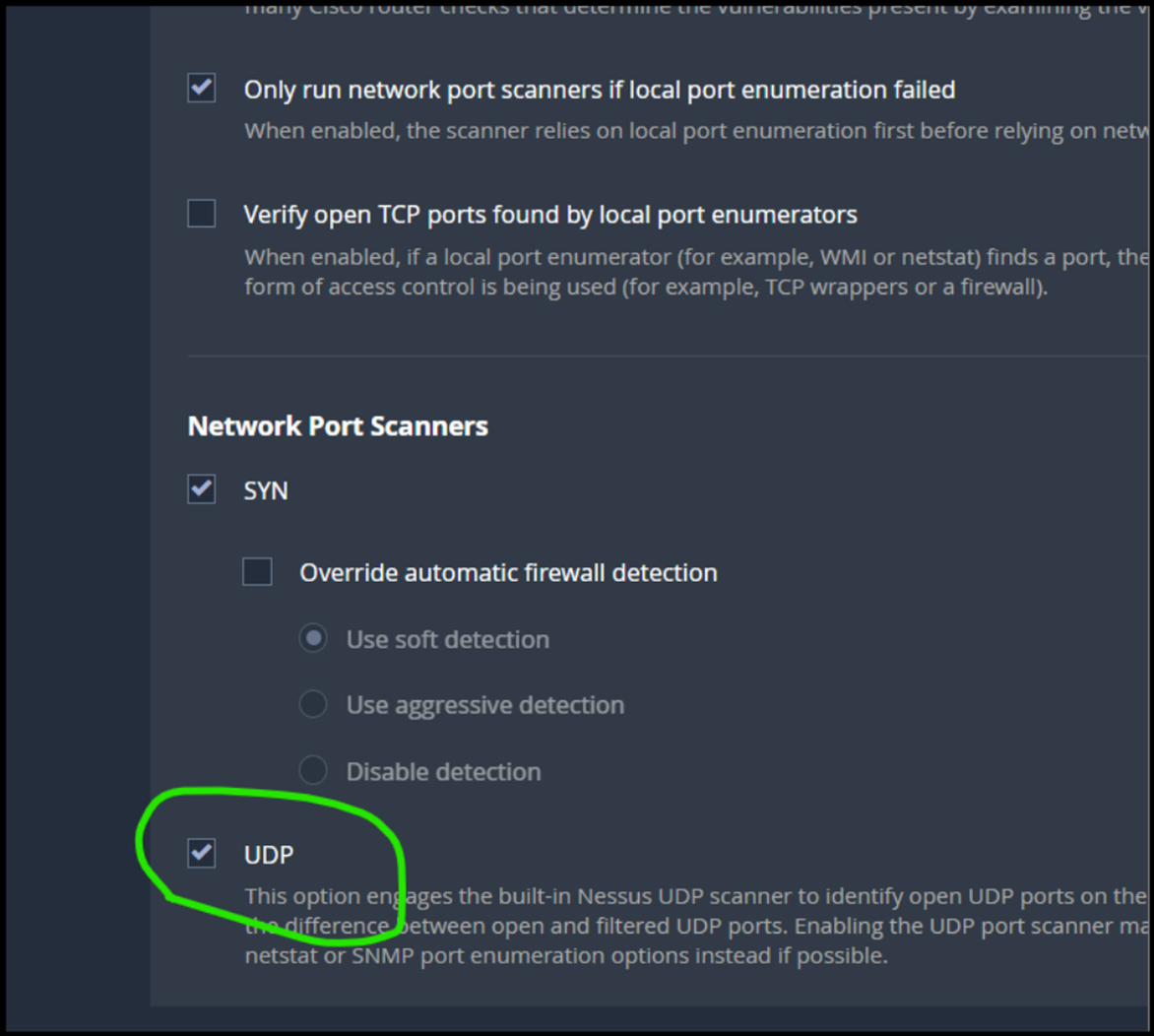
turn on the UDP
-
in port scanning : set port scan range
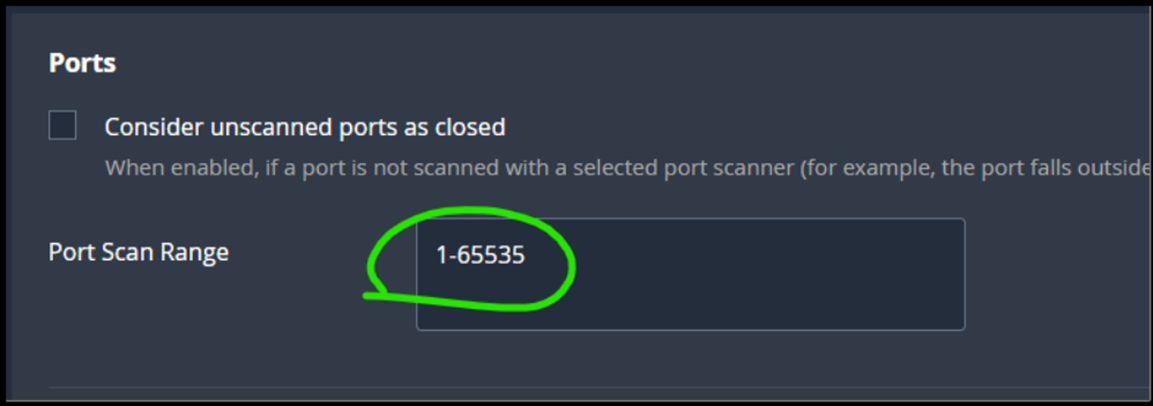
-
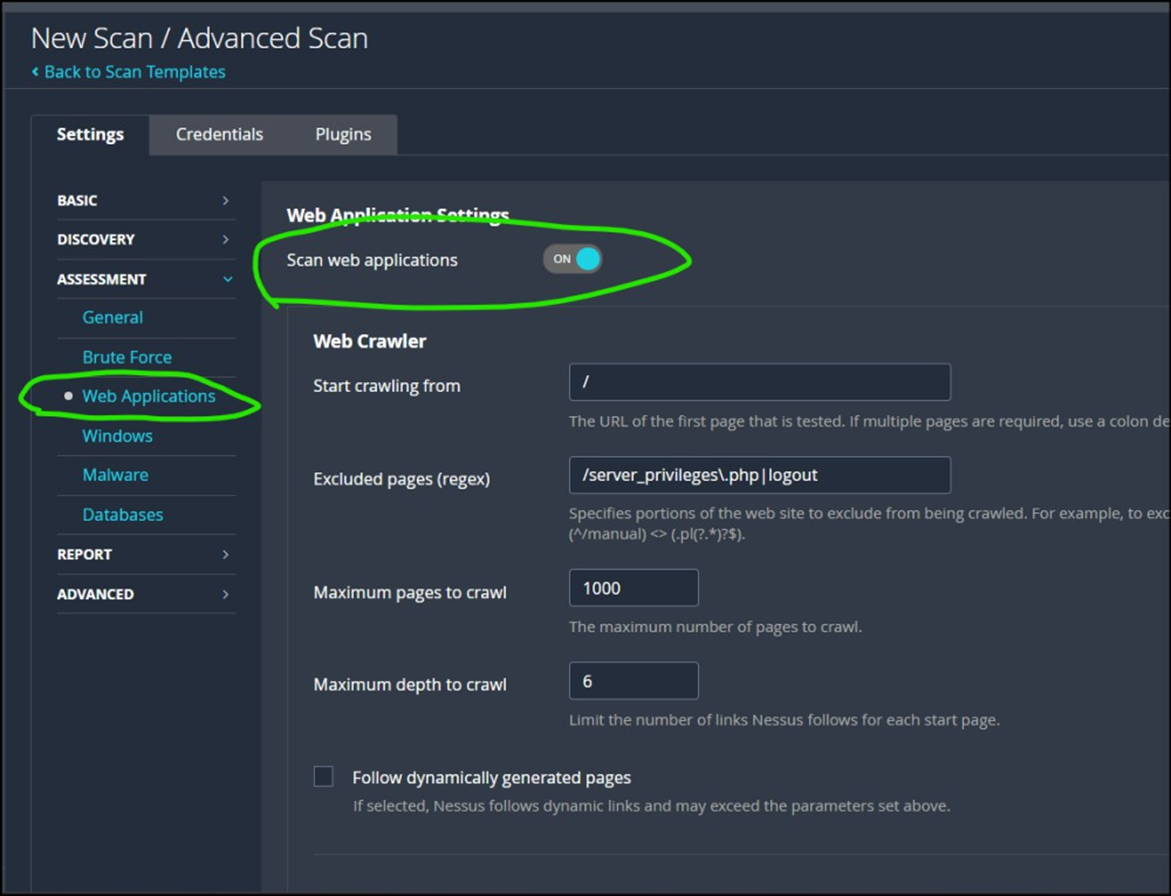
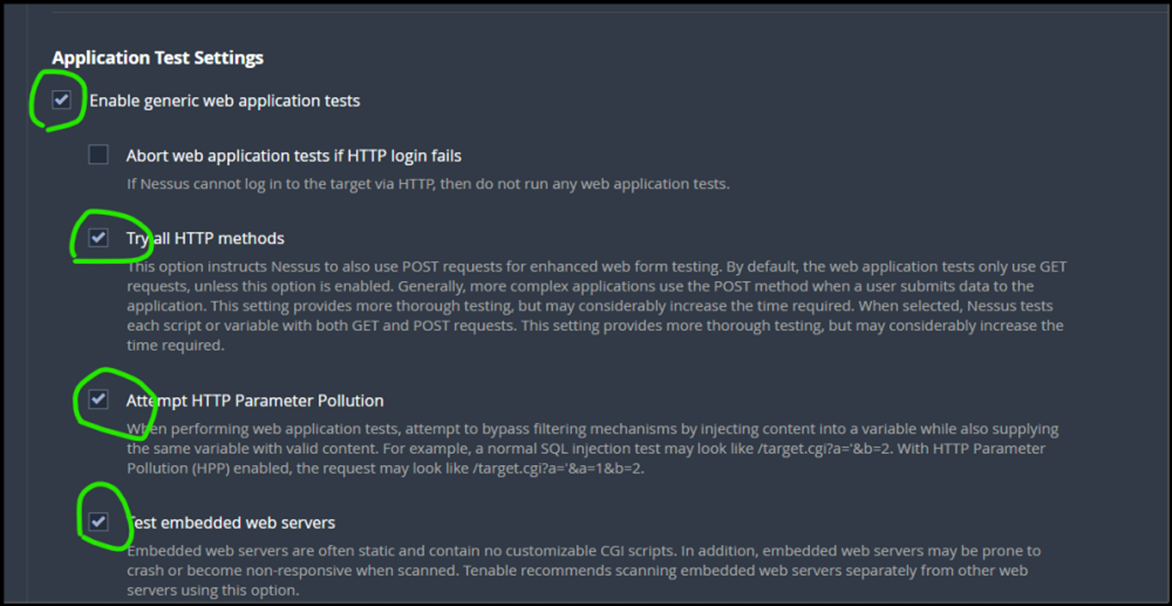
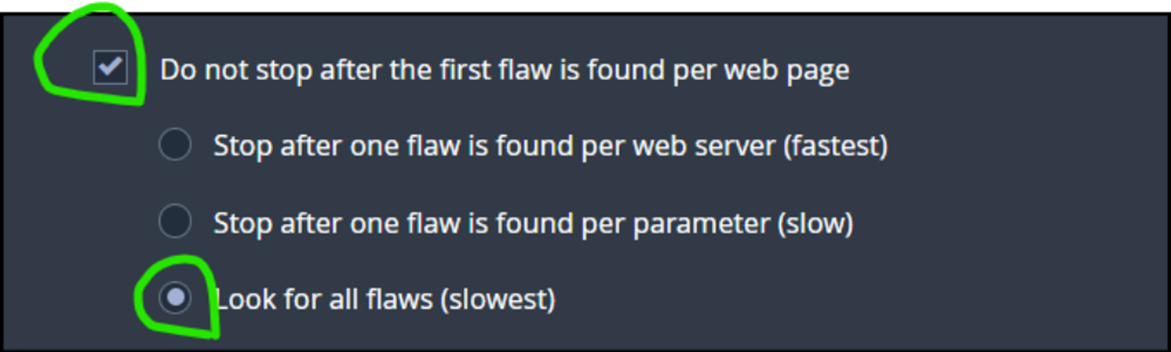
Web applications → do the following edits
-
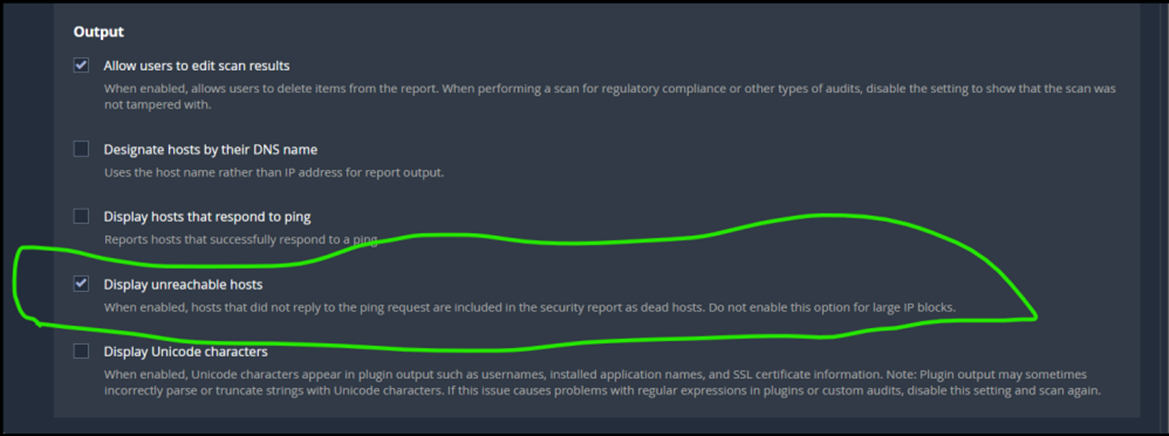
Go to
report
! 900
-
go to
advanced→ enable the safe checks
if its enabled , jo server ko crash karne wale plugins hai woh server ko crash nehi karega.
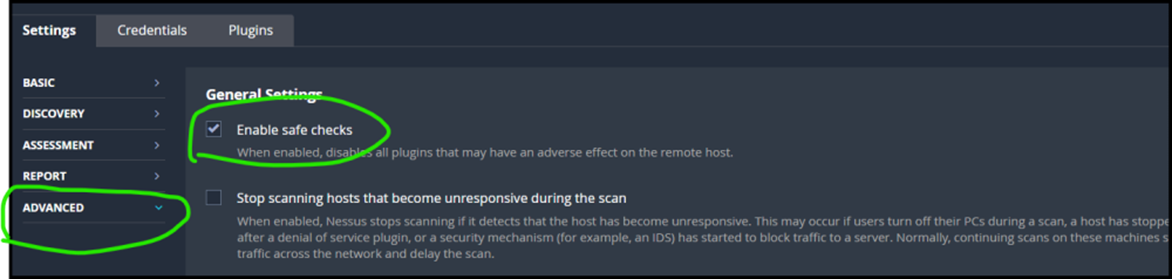
! 900
-
go to
Credentials→shh
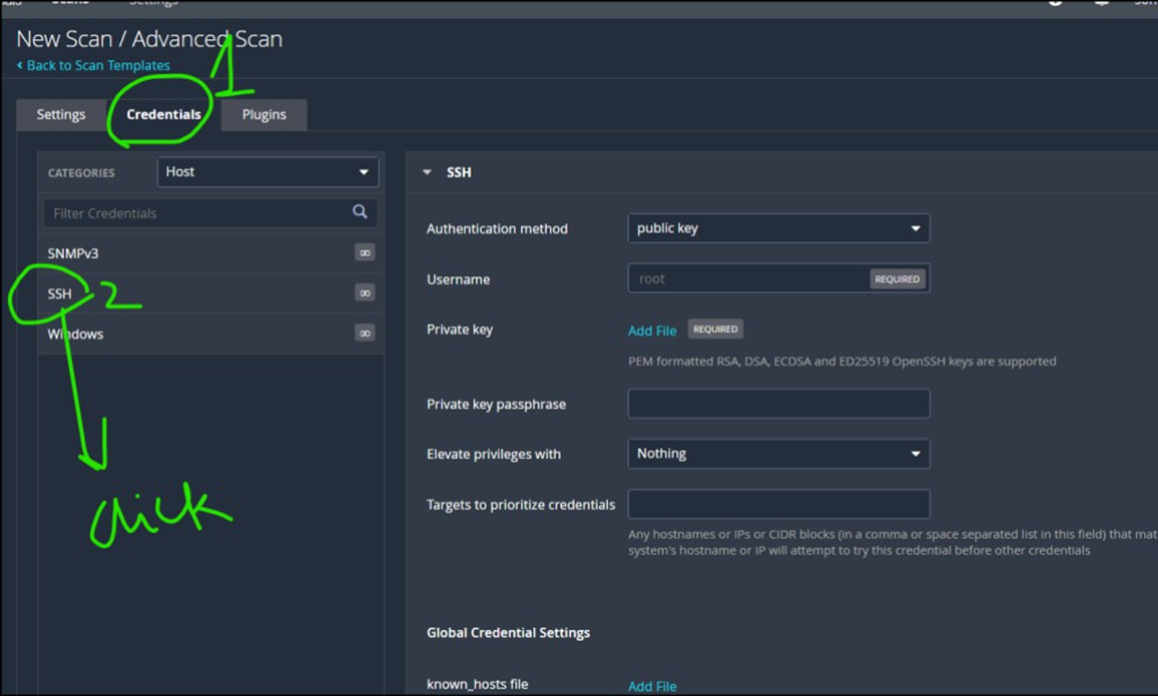
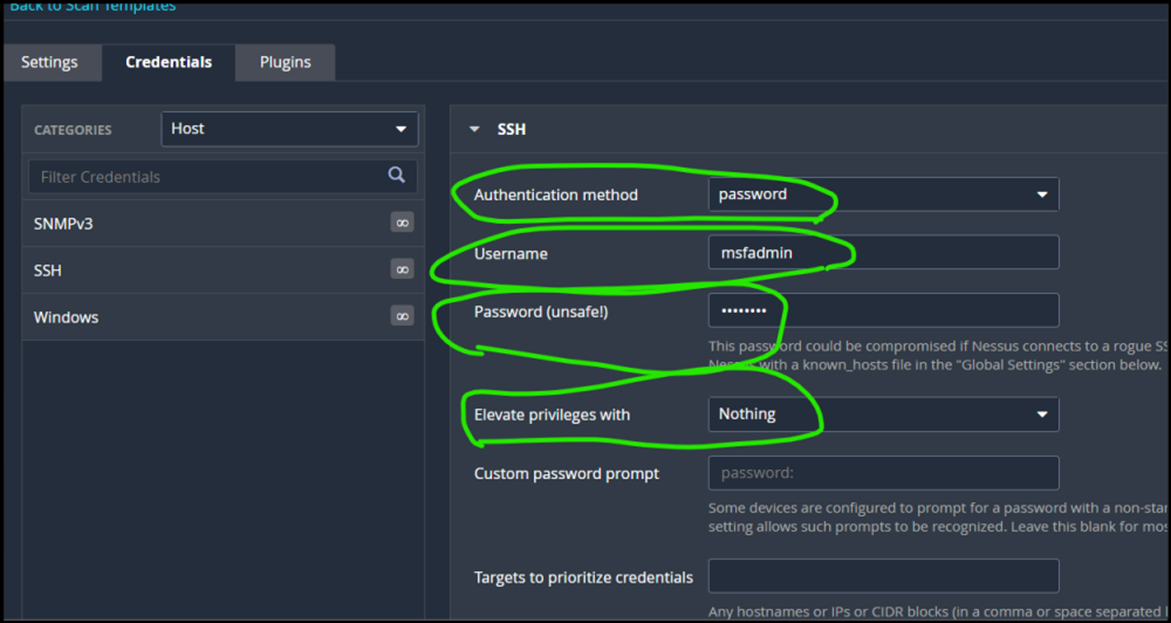
-
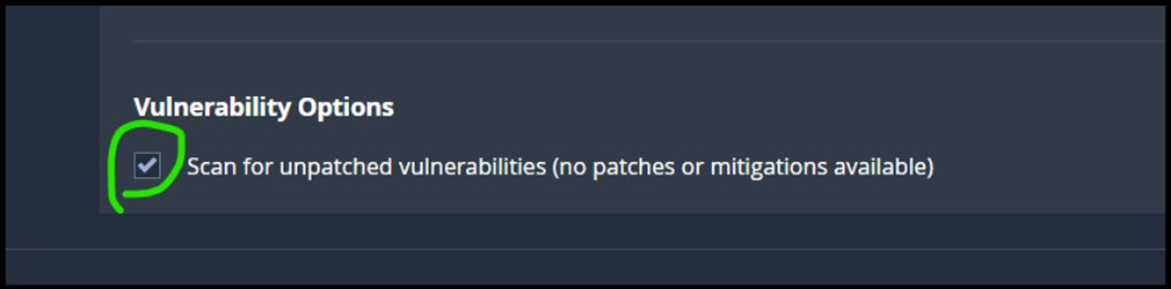
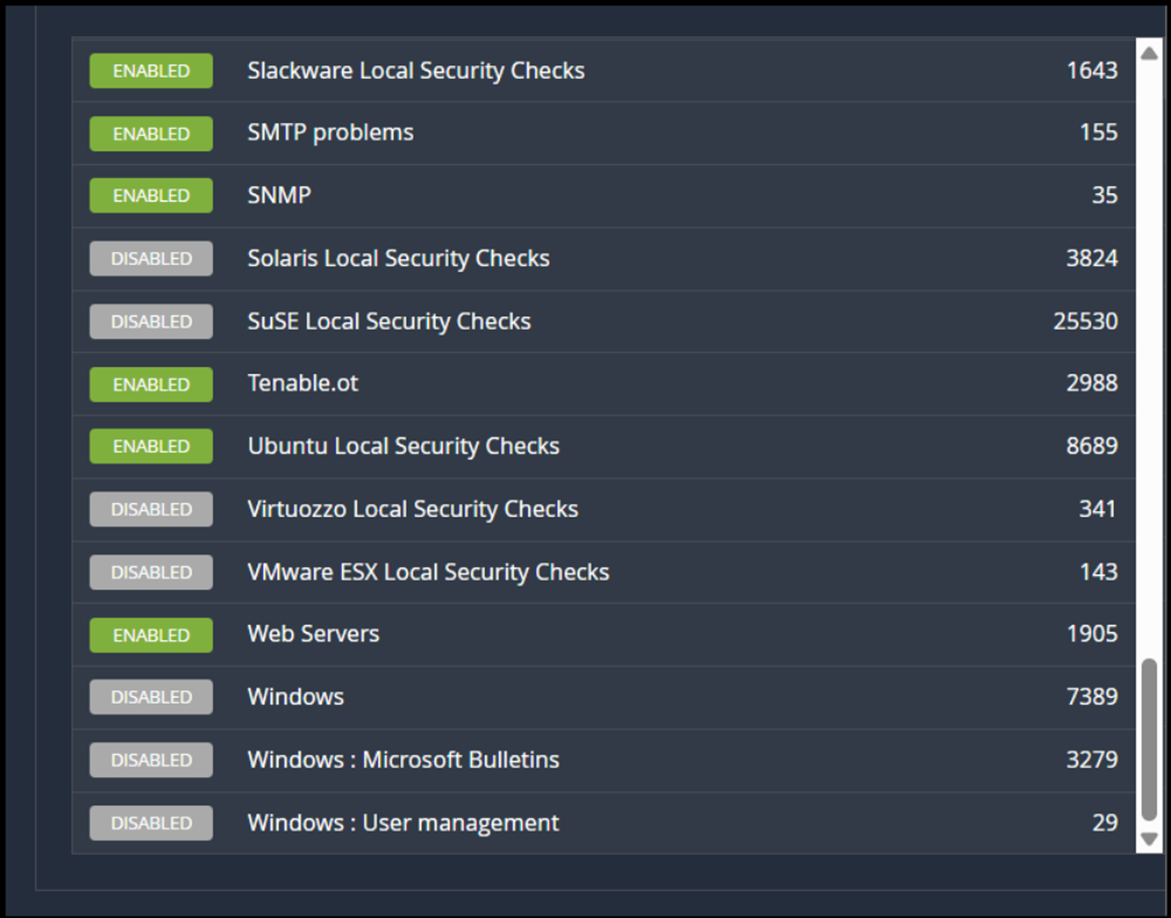
go to plugins and disable the following
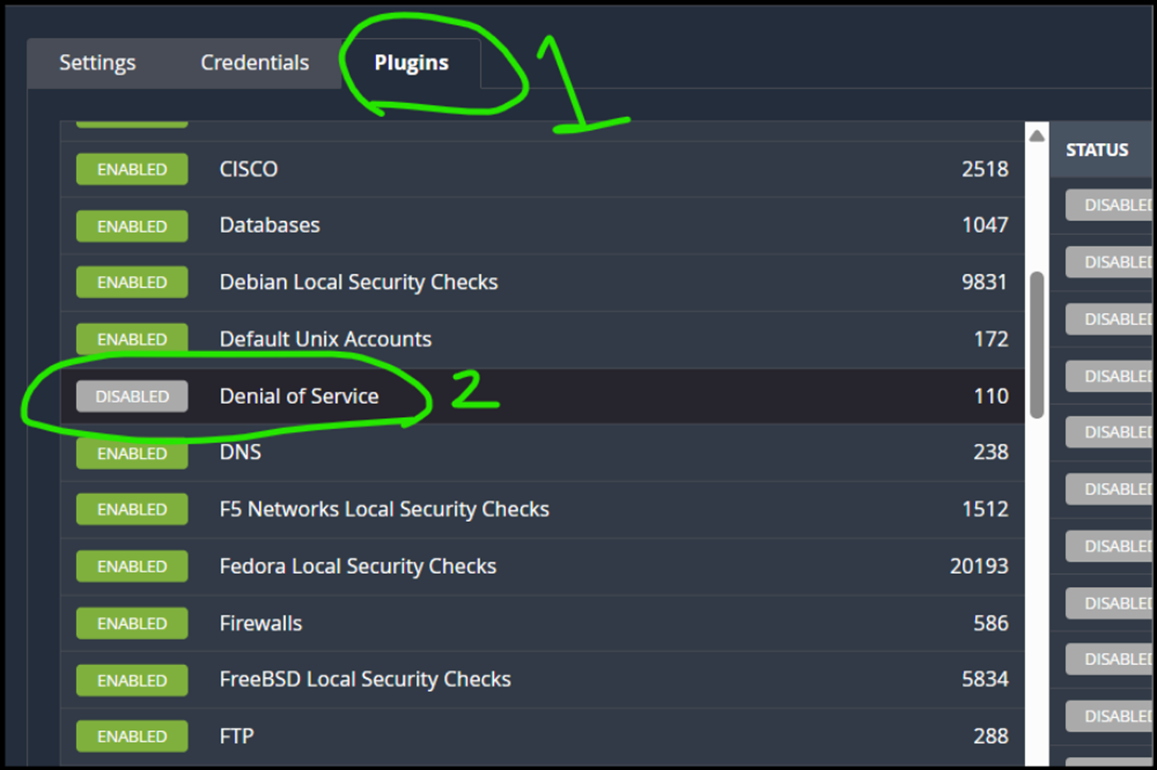
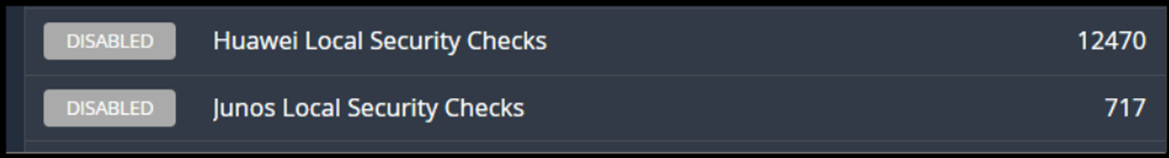
! 900
-
Save
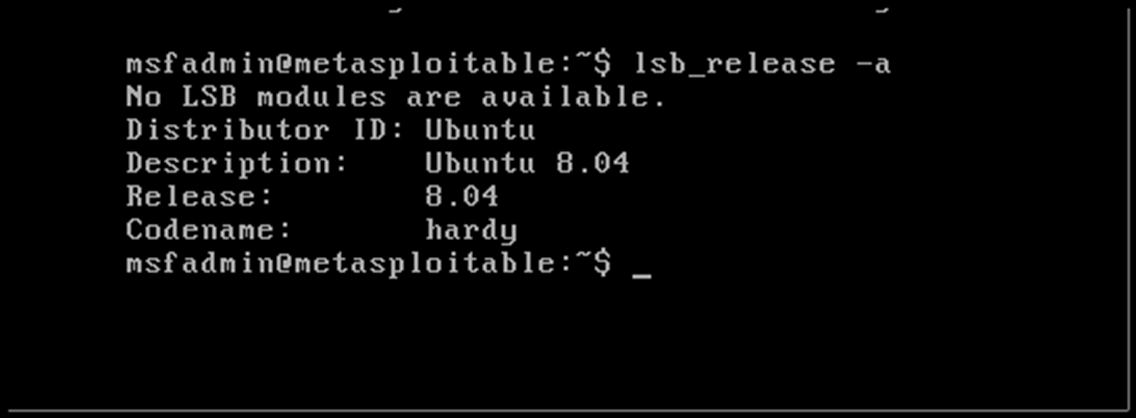
- In metasplotable-2, hit the following command to know the target os
Burp Suite — Web App Hacker Tool
-
Think of it as a hacker's magnifying glass for websites.
-
It helps you test if login forms, search boxes, etc. can be hacked.
-
You can see and change the data sent between browser and website.
-
It’s used for testing things like:
- Login bypass
- XSS (cross-site scripting)
- SQL injection
- Hidden bugs in web pages
Used by: Web security testers (manual testing)
Nessus — Network Scanner
-
Think of it as a security guard checking if your computers and servers have known problems.
-
It scans for:
- Weak passwords
- Outdated software
- Open ports that hackers could use
- Known vulnerabilities (CVEs)
Used by: IT teams and companies (automatic scanning)