https://www.fatalerrors.org/a/dvwa-customsguide-sql-injection-blind.html
1️⃣ What is Blind SQL Injection?
- It is like normal SQL Injection, but we do not see errors or database output on the webpage.
- Instead, we check how the website responds (like different messages or slow response times).
2️⃣ How does it work?
- Instead of error messages, we see generic messages (e.g., "User ID exists" or "User ID is MISSING").
- The attacker asks True/False questions using SQL.
- If the page changes its response or takes longer, the SQL query worked.
3️⃣ Time-Based Blind SQL Injection
- If there is no visible change, we use a time delay query to confirm injection.
4️⃣ Low-Level Security in DVWA
- The GET method is used to send user ID in the URL.
- The input goes directly into the SQL query without filtering.
- The website does not show SQL errors, only a message like:
--> ✅ "User ID exists in the database" (Query successful)
--> ❌ "User ID is MISSING from the database" (Query failed)
Lab
-
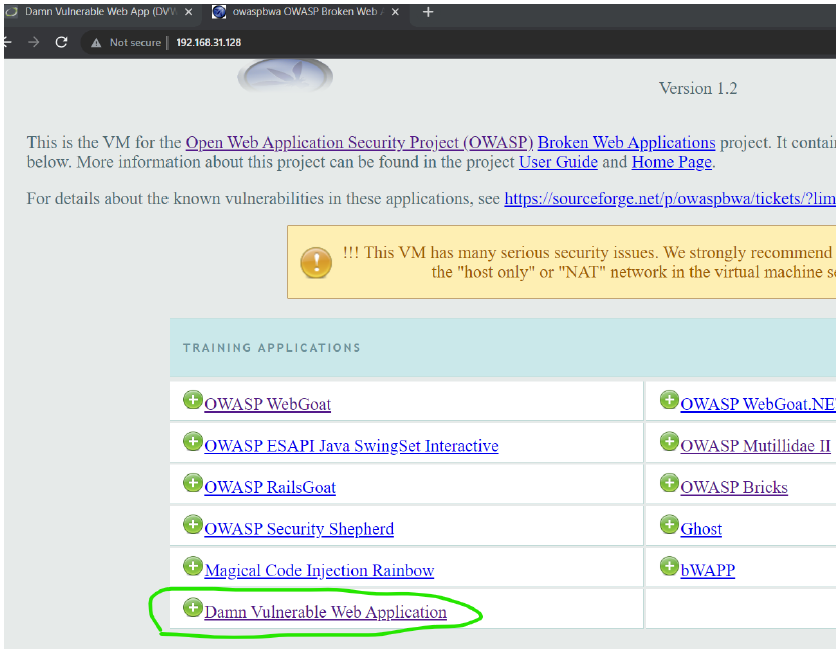
open owasp → then hit the ip in burp's browser → DVWA → username : admin ,password:admin → then go to sql injection (blind)
-
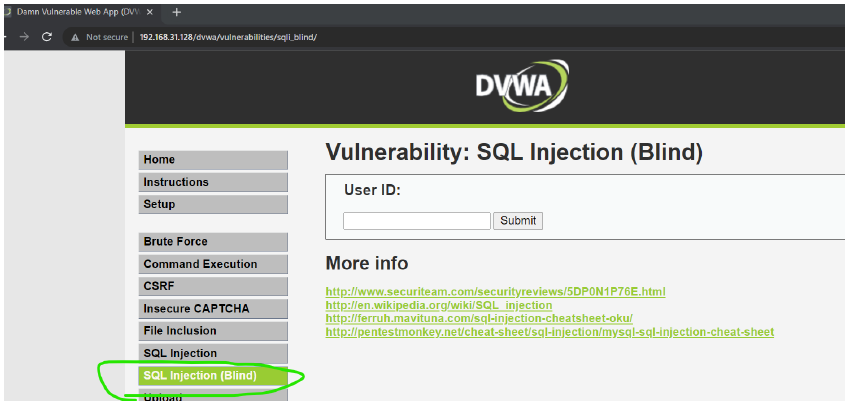
click on sql injection(Blind)
-
What Happens?
- Since 1 = 1 is always TRUE, the query executes successfully.
- The database returns valid user information (e.g., admin, admin).
- This confirms Blind SQL Injection and shows that we can manipulate queries to extract data.
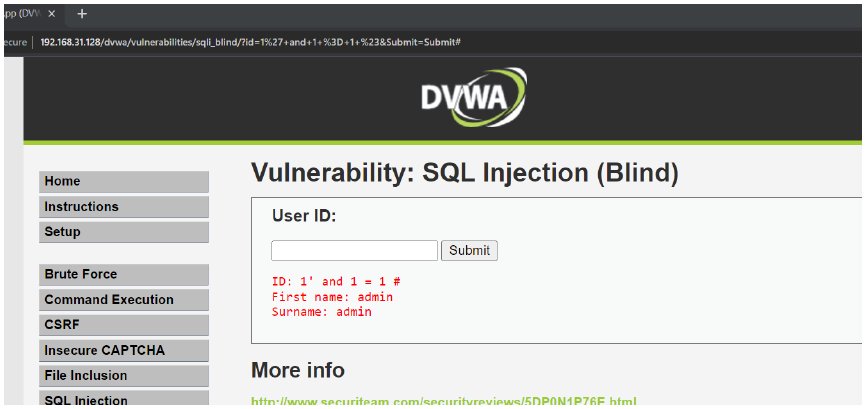
- 1' and 1 = 2 #
nothing is happening because
- The SQL query fails because 1 = 2 is false.
- The page shows "User ID is MISSING" → confirming Blind SQL Injection.
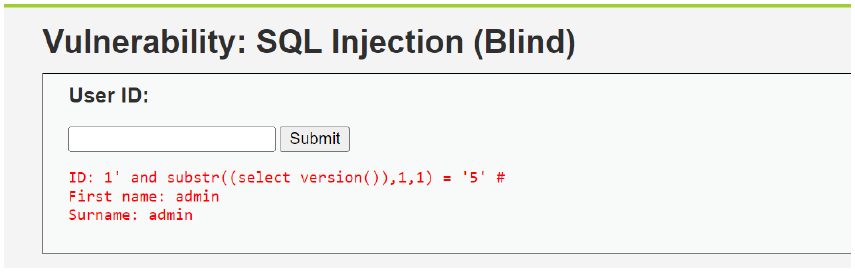
- substr((select version()),1,1) → Extracts the first character of the version string.
- = '5' → Checks if the first character is '5'.
- If the query is successful ("User ID exists"), then the first character is confirmed as '5'.
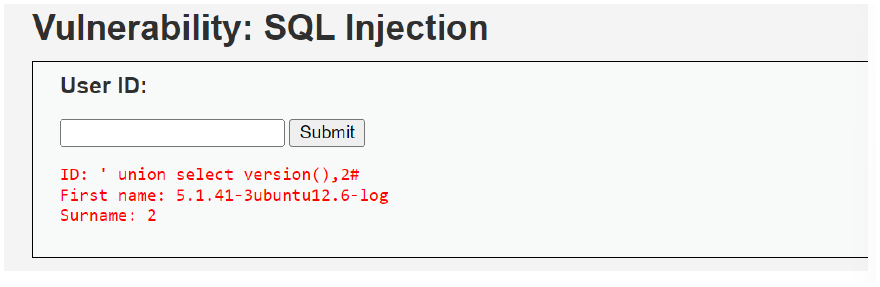
- ' union select version(),2# → to know the version of the sql used.