There are 3 type of Hashing algo in windows:
1. LM(LAN Manager)
- It is an encryption mechanism used by Microsoft before it released NTLM.
- It was meant to be one-way hash, but later failed
- Here, user enter credentials on a workstation and encrypt it.
- Password was padded to 14 bytes.
- Each 7 bytes half is encrypted with DES with separate keys.(This makes it weaker)
- It is susceptible to brute force attack.
A one-way hash function is an algorithm that takes an input (in this case, a password) and produces a fixed-size string of characters, the "hash." The core principle of a one-way hash is that it should be computationally infeasible to reverse the process—that is, to figure out the original password from the hash.
However, while the LM hash was intended to be one-way, it is critically flawed and considered broken by modern standards. Due to its significant cryptographic weaknesses, it is practically reversible.
- NTLM(New Technology LAN Manager)
-
Two versions :
-
NTLMv1
- was developed by Microsoft
- It supports both old and new Windows version
- It is also vulnerable to brute-force because it uses a weak DES encryption algorithm that is fast to decrypt.
-
NTLMv2
- uses the same flow as NTLMv1 but has 2 changes
- The client includes a timestamp when it sends the user name to the client
- The targeted server generates a variable-length challenge
- These changes help mitigate relay attacks
- And yet, NLTMv2 is still exposed to other NLTMv1 vuln since it is still using the same authentication mechanism.
- uses the same flow as NTLMv1 but has 2 changes
-
-
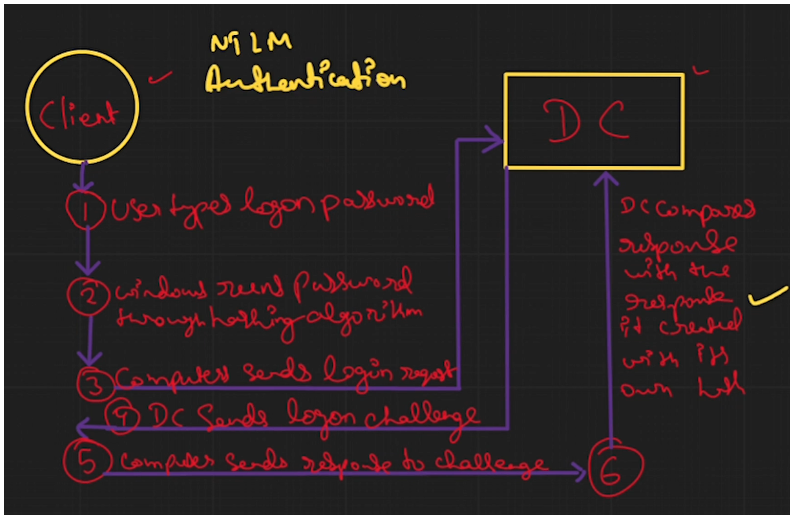
NLTM follows challenge-response mechanism
- User sends its password and also sends the challenge-response
- If both the things are correct, then the DC will authenticate it and the user will be login
-
- 
- After this also, NTLM is vuln to:
- MITM attack
- Pass-the hash attack
- ...so on
NTLM Authentication
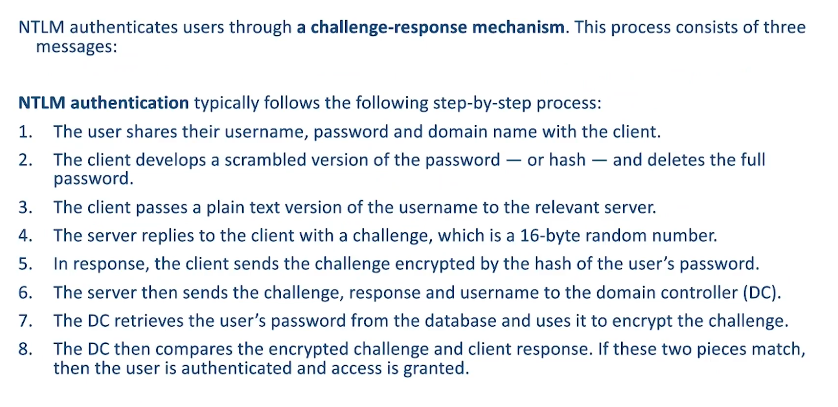
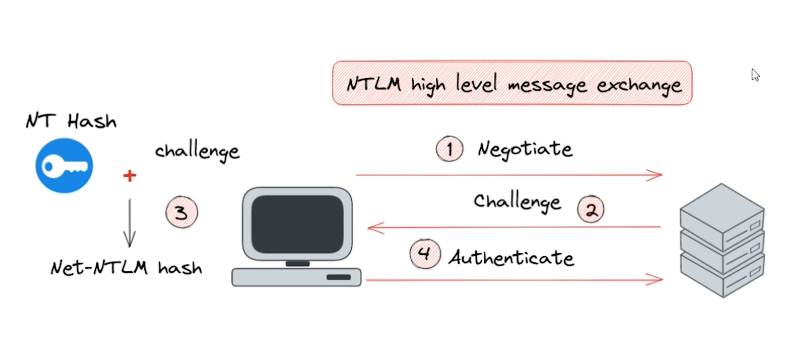
- NTLM Authentication Diagram
3. Kerberose
-
(it is not exactly a hashing algo, it is a network authentication protocol used in AD)
-
a default authentication service for Microsoft windows domain. (a network authentication protocol)
-
intended to be more "secure" than NLTM by using third party ticket authorization as well as stronger encryption.
-
currently version 5 of kerberos is used
-
The Kerberos Key Distribution Center (KDC) uses the domain's Active Directory service database as it's security account database.
-
Authentication is based ticketing system.