- find out what are the software or component versions being used at the target system.
- web app or server or any dependency libraries
- we usually search publicly available exploits
- search inside central vulnerability repositories like Exploit-DB , Github , NVD , CVE etc.
- then analyse the exploit scriot
- try to modify the script, if required
- finally execute the script
- mostly this kind issue led us to RCE i.e server takeover
- check if any software component is obsolete or out-dated.
Note :
To assess the security of a target system, begin by identifying the versions of software and components in use, including web applications, servers, and dependency libraries. This information helps determine potential vulnerabilities. Next, search for publicly available exploits in central vulnerability repositories such as Exploit-DB, GitHub, NVD, and
the CVE database. Once a relevant exploit is found, analyze its script to understand how it works. If necessary, modify the script to suit the target environment. After making adjustments, execute the exploit to verify its effectiveness. In many cases, such vulnerabilities can lead to Remote Code Execution (RCE), potentially allowing complete
server takeover.
Additionally, check if any software components are obsolete or
outdated, as these often contain unpatched security flaws that
attackers can exploit. Keeping all components updated is
crucial for maintaining system security.
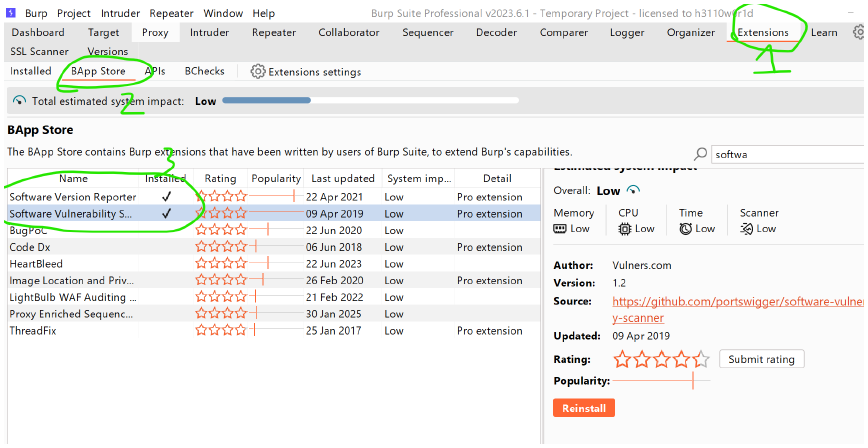
Step 1 : install both s/w version reporter and s/w vulnerability scanner
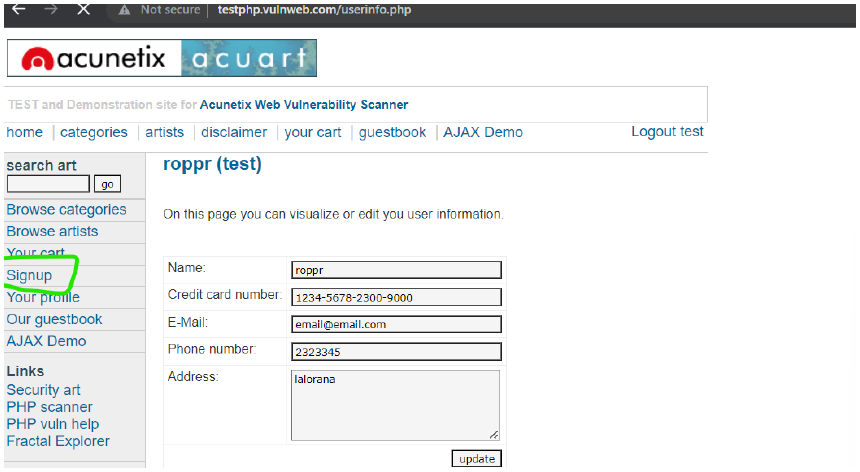
Step 2: go to this site -> signup -> login by username : test ,passwd : test -> intercept on -> refresh the login page of website
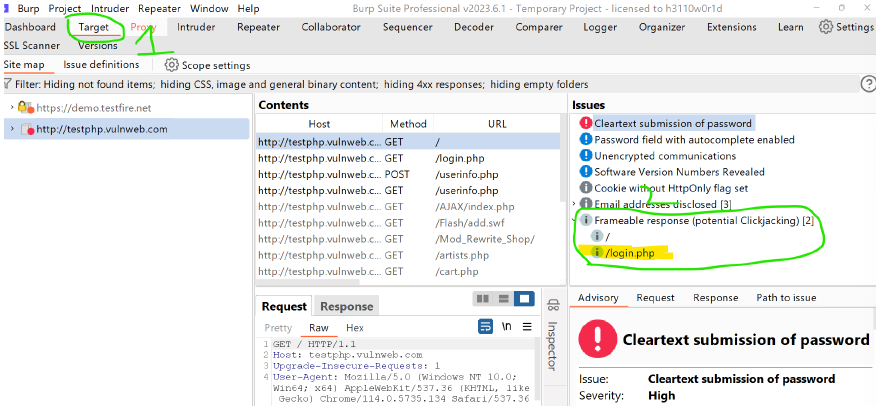
Step 3 : go Target, you can see the login.php